Fortinet FortiGate FG-40F Performance and Security Testing
For this, we are using our high-end Keysight CyPerf testing machine, with our STH traffic profiles that you have seen on a number of STH reviews so far. The machine itself is able to generate over 2Tbps of traffic, and we use it mostly now for our L4-7 network testing since we have the multi-XGS2 chassis and line card setup for L1-3 and switches. One of the cool parts about our setup, if you have seen previous reviews, is that the gateway devices and firewalls being tested look like real traffic. To be clear, we have a setup designed for really high-end 400Gbps and 800Gbps gear, so running it to test a 1Gbps gateway is more than just a bit of overkill.
First, we ran a simple bidirectional throughput test to verify that the FortiSOC4 can handle line-rate traffic. Realistically, just passing LAN-WAN 1Gbps traffic is not a hard workload, but this is also not the newest gateway device out there.

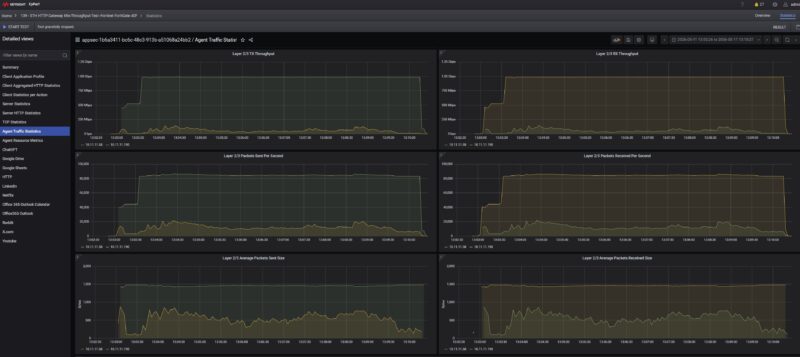
We saw fairly close to line rate at L2/3 and around 1.85Gbps on L4/7, which is also about line rate. We then switched to our STH gateway device 11 app mix of ChatGPT, Google Drive, Google Sheets, LinkedIn, Netflix, Office365 Outlook and Calendar, Reddit, X.com, and YouTube:
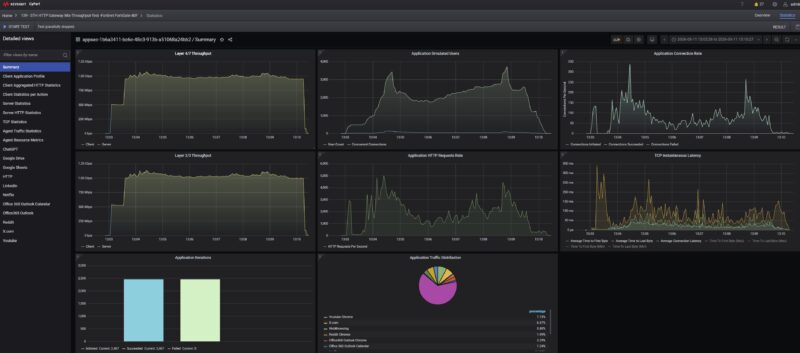
That is more of an unidirectional test, but you can see that we are getting around line rate as well. This is exactly what we have come to expect from gateway devices. Frankly, if you are just NAT’ing traffic at 1Gbps speeds, the FG-40F is overkill.
That, of course, was with the firewall off. Fortinet, however, is a premium brand because it offers various security features, not just a basic firewall.
You may have seen that we have our own STH attack profiles. Some solutions do well, others, like the TP-Link Omada VPN Gateway ER8411, we could not get to block attacks. The experience with the FG-40F was very different. As we showed earlier, Fortinet offers a firewall and features such as flow-based inspection, deep SSL/SSH inspection, high-security IPS, application control, antivirus, web filtering, DNS filtering, email filtering, DLP, file filtering, virtual patching, and UTM logging.
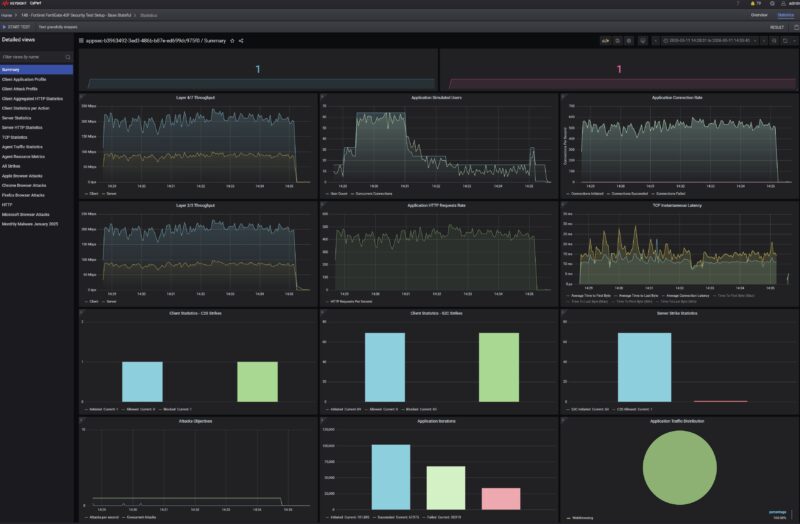
The impact was noticeable on two fronts. Performance certainly dropped from our 1Gbps baseline when these features were turned on, but at the same time, unlike with the base Ubiquiti UCG-Fiber (note we tested the base, no-subscription version back then), TP-Link, and other routers we were testing, the FG-40F destroyed this test. In the test above, only one attack got through, and it was an old Apple CVE. Still, that is really good. Sure, the throughput is way down, but from a straight security standpoint, this is what we want to see. Once we started adding features, we were in the 99.4%+ block rate, which is the best we have seen by far.
The next question is important. What happens when you turn on Fortinet’s features to enable higher levels of security?
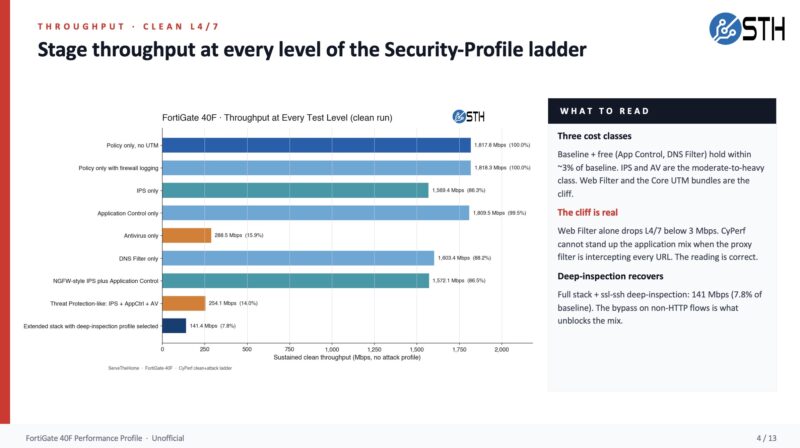
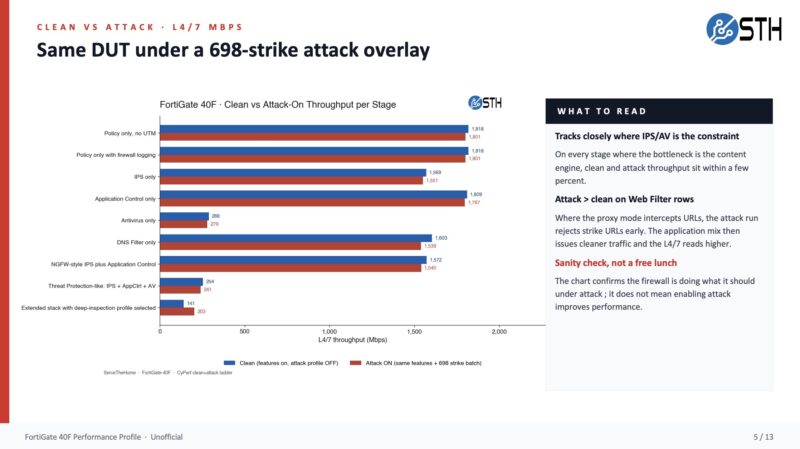
We went through the exercise of turning features on and off and trying to quantify how much of a performance impact we saw. Antivirus seemed like a big hit compared to the others. Here is a quick look at when we had the attack profiles on versus off.
Part of the reason for doing this is that folks often say they see vendor claims and apply a scaling factor, often 30-60%, to do sizing for their own workloads. We were closer to Fortinet’s spec sheet with our numbers, often a small percentage off, which was an interesting finding in itself.
There are many things we still need to work through. One example is that we are generating so much data now that we need to figure out how to present it, since most folks do not have the appetite for 50-100 pages of data. We are also using default profiles, and our reviews are generally done as a point in time, but firewalls evolve over time. Still much work to do, which is why we are starting with a more well-seasoned batch of gateway devices. One other major gap we have right now is VPN performance. That is something I am hoping we can add in the second batch of reviews, likely kicking off in Q3 2026. Lots of work still to do.
Fortinet FortiGate FG-40F Power Consumption and Noise
Fortinet has a 12V power adapter that can use different socket adapters. This allows one SKU to be used across different countries.

We generally saw 5-5.6W at idle, which is very good. As a fanless unit, it is also silent.

Fortinet says the average power consumption is 7.74W with a maximum of 9.46W, making this a very low-power device. That is one of the advantages of spinning your own silicon.
Final Words
I first contacted Fortinet in 2013, went to the company’s old HQ in Sunnyvale, and tried kickstarting firewall reviews. That went decidedly nowhere, even though we had purchased a unit to use at the time. Now we have better tools and a bigger team, so I think we can do a solid job on bringing the industry’s gateway devices (sub-2Tbps) into a more standardized review process. The Fortinet FortiGate FG-40F is a neat little unit for those who need a 1Gbps-capable firewall. We also tested the FG-60F in this round. As you might expect, that one is faster and has more ports. These devices offer a ton of features and are relatively easy to use and deploy. Well, easy once you get past the licensing and onboarding hurdles.

To be fair, we are using the FG-40F here because it is an older model, so we figured that would be a good place to start the series. We have a bunch of devices from several vendors already in progress. Our hope is to shed more light on this segment of the market since we often see these devices in our AI data center and lab tours. Overall, it was really neat to see all of the engineering, down to the custom silicon, that Fortinet puts into these firewalls.
Where to Buy
If you want to purchase one of these, here is an Amazon affiliate link.



I can’t wait for y’all to do more firewall reviews. Talk ’bout an opaque industry.
Any chance you will review the Watchguard Firebox M-Series (M270, M290) ?