Fortinet FortiGate FG-40F Software Experience
Logging in, Fortinet’s default IP is 192.168.1.99, and the default username is admin with no password. You are immediately required to change the password.
We logged into our unit, and saw the FortiOS 7.2 dashboard.
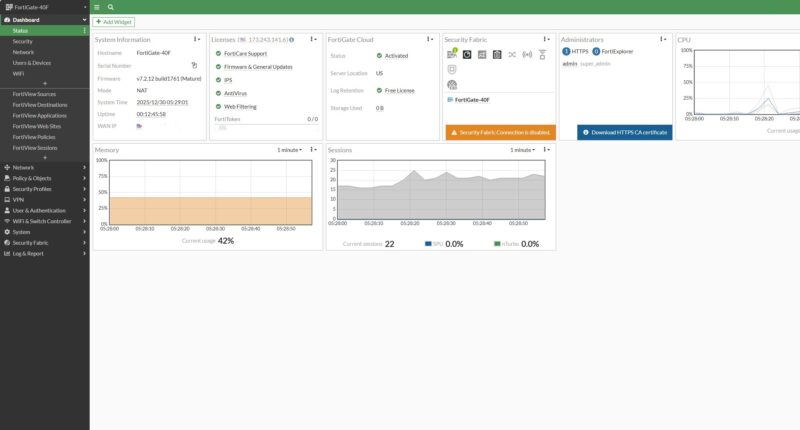
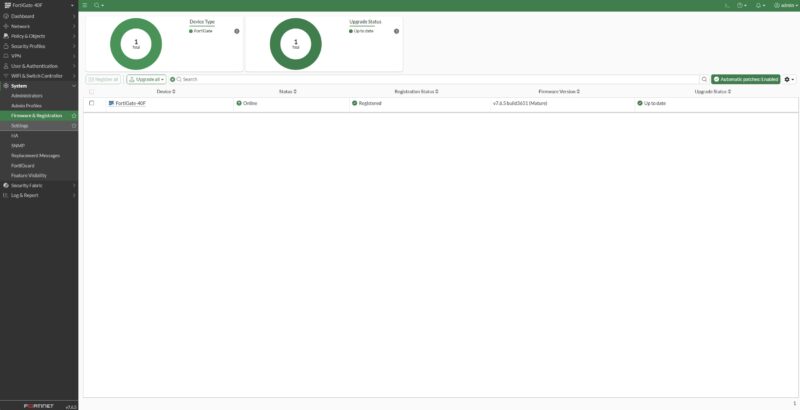
Fortinet has various firmware lineages but keeping up to date is very important.
So we upgraded to FortiOS 7.4.
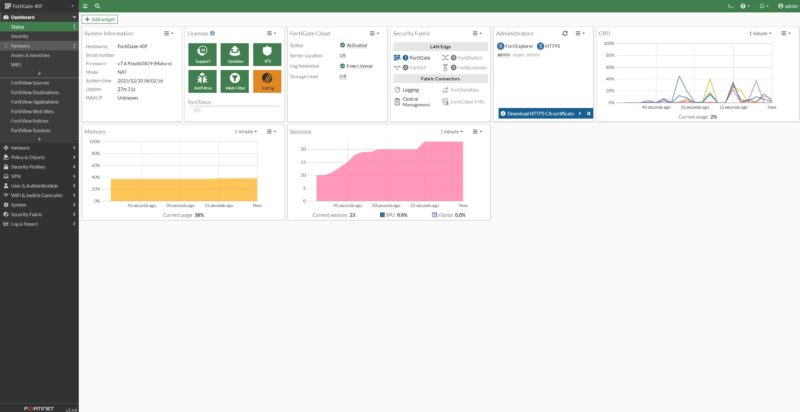
Then to FortiOS 7.6.
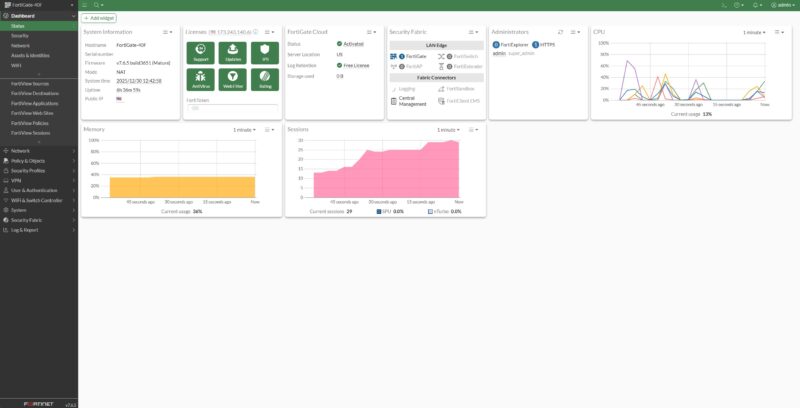
Just a quick note: we ended up testing on FortiOS 7.6.6, but the screenshots you will see are from FortiOS 7.6.5. It took a bit of time to put this all together and test other firewall brands at the same time, so we ended up re-testing on the newer firmware version.
Once you are set up and have registered your device, there are UIs and wizards for a ton of features. The interface setup is relatively intuitive, and Fortinet has the gateway diagram with port labels and connection status on top. If you configure hundreds of these, you probably do not notice little features like this.
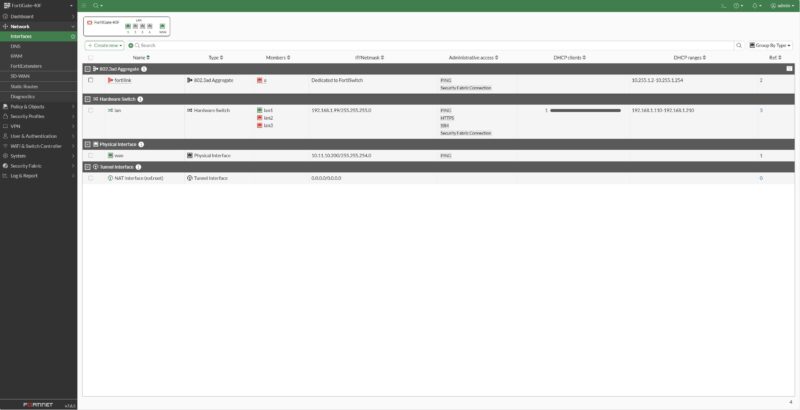
Setting the box up, there is a “FortiLink Interface” which some may not know. This is a link to discover FortiSwitch devices and help automate networking.
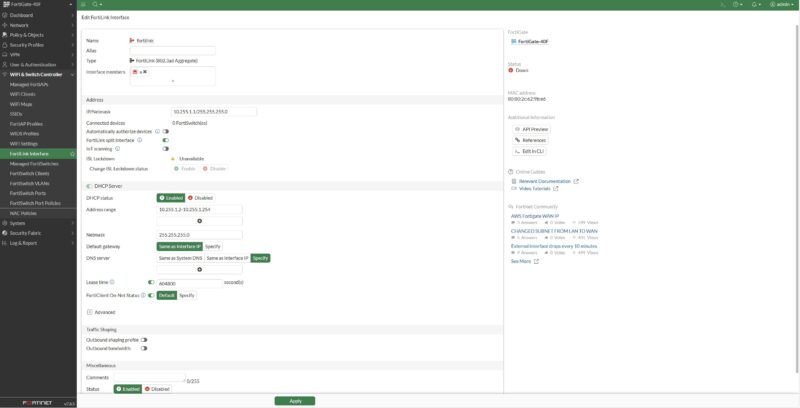
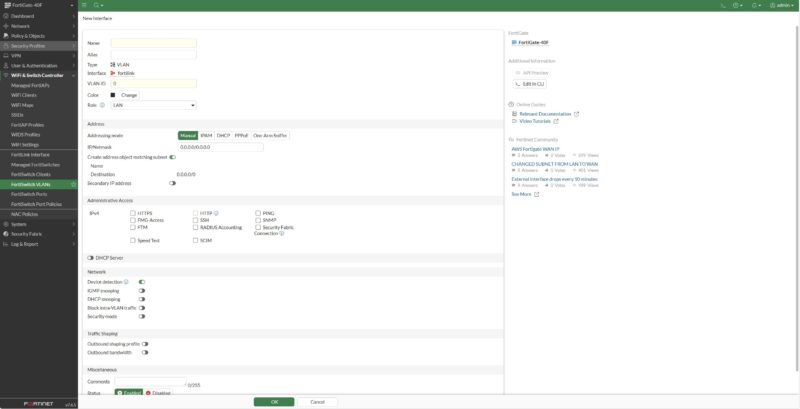
Here, you can do things like set up FortiSwitch VLANs from the gateway as well. We only have two FortiSwitch devices, but expect reviews of those on STH.
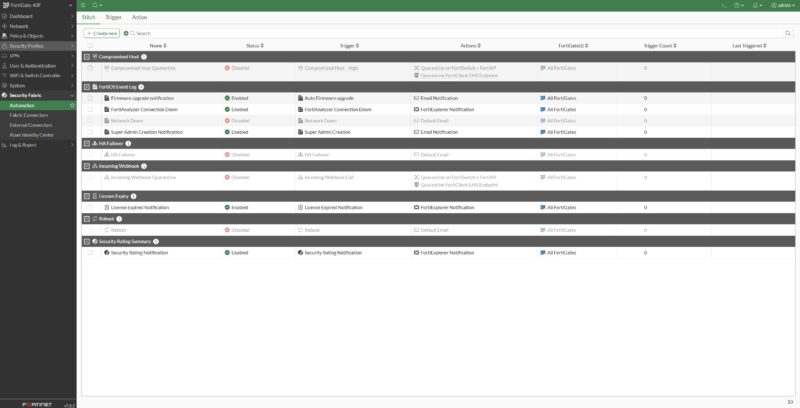
There are workflows for security fabric automation and many other common tasks.
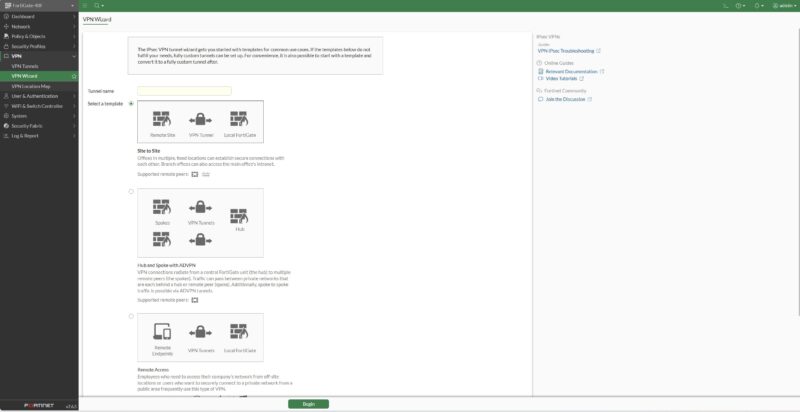
VPNs are a big deal for Fortinet and this entire segment. It turns out that both CyPerf and IxNetwork, which we use, have great VPN testing tools, but we are going to add that into future reviews.
On the security side, Fortinet is well known for its security features including its IPS.
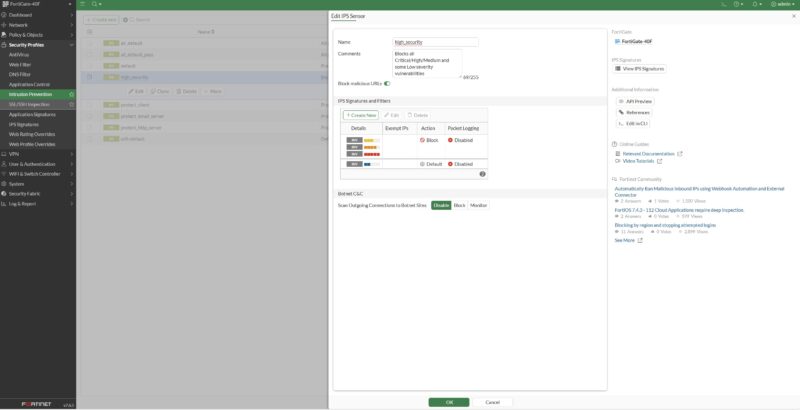
With a subscription, you have access to a great default set of IPS signatures. We will look at the performance of turning many of the security features on in our performance testing section.
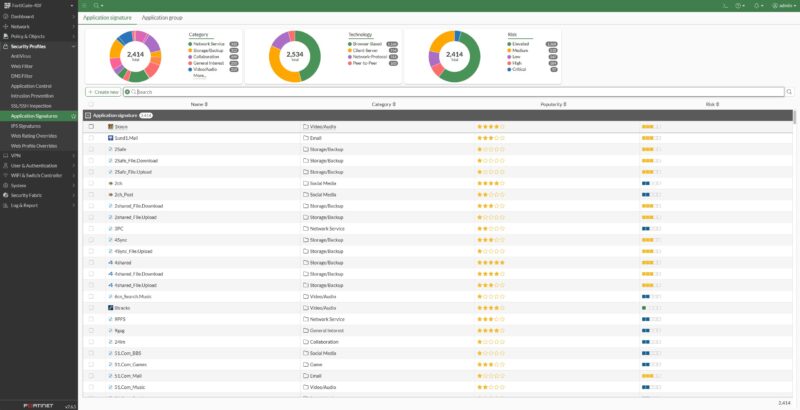
There is an application sensor feature as well.
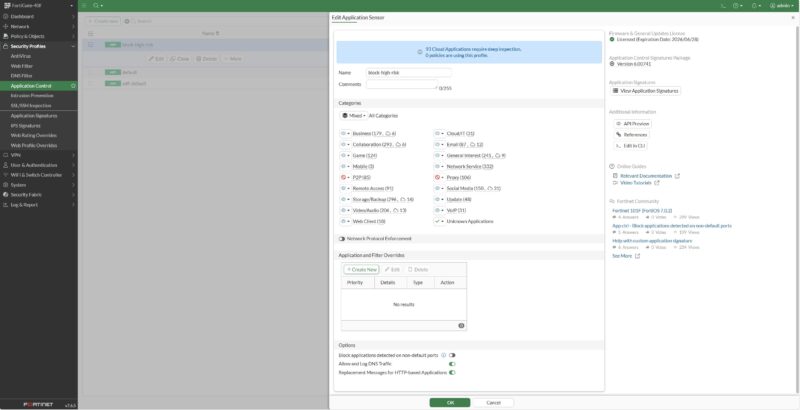
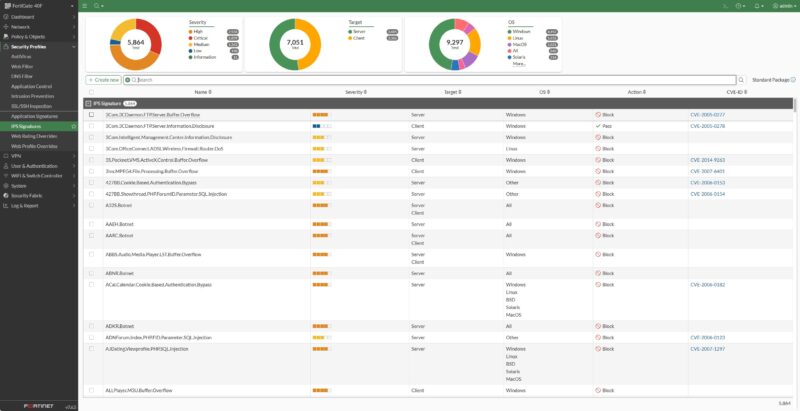
Here is a quick look at the signatures for that:
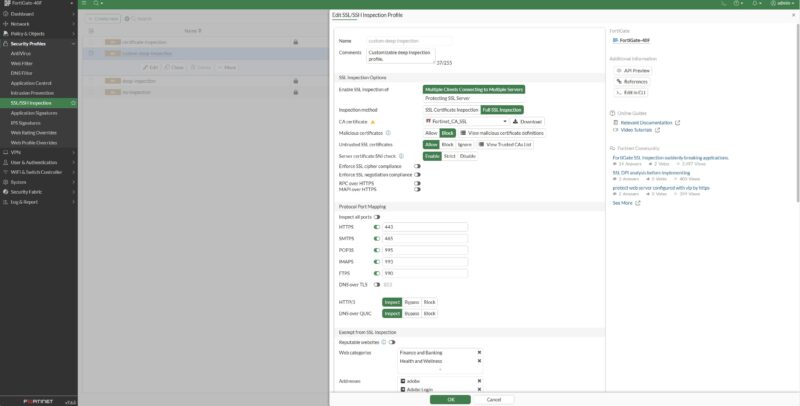
Fortinet also has SSL and SSH inspection features.
There are, of course, web filters.
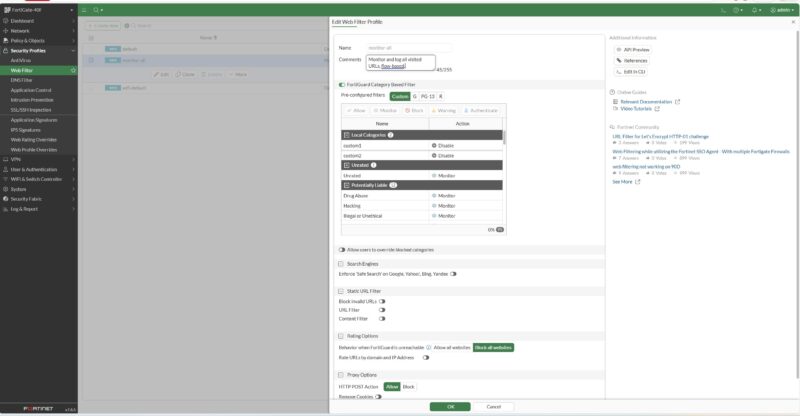
To be clear, there are a surprising number of features here, and they are fairly easy to configure. Many will benefit from fine-tuning, like the web filter.
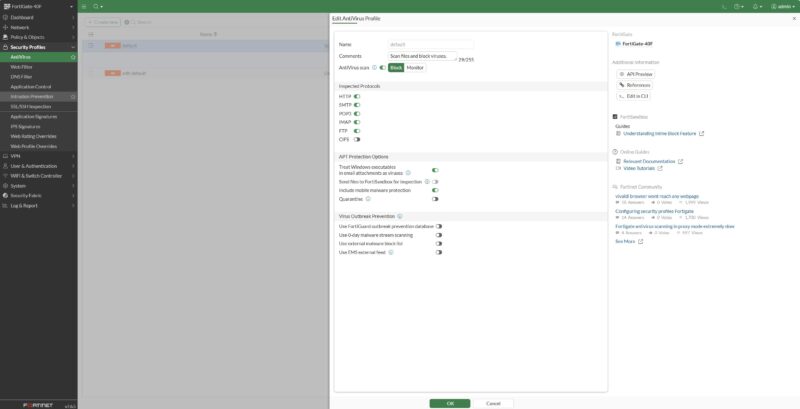
A final one for this round of highlights is the AntiVirus feature.
There is a CLI for Fortinet, which is how we did most of the configuration of these units.
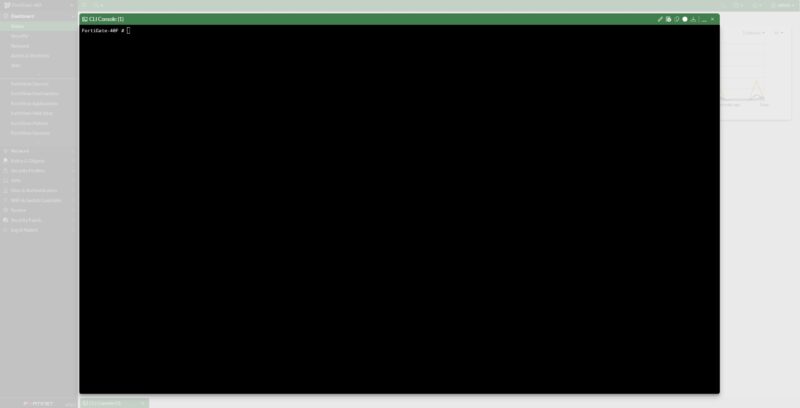
On both the FG-30G (both units) and FG-60F we ended up having to use the console port to fix firmware updates or to fix an update gone poorly. That was not in play here, as SSH login and gateway configuration were easy enough. Since we did all the performance testing for these boxes back-to-back, we ended up using console access on three of the four boxes on hand just to update firmware, so it is an important feature.
A Word on Onboarding
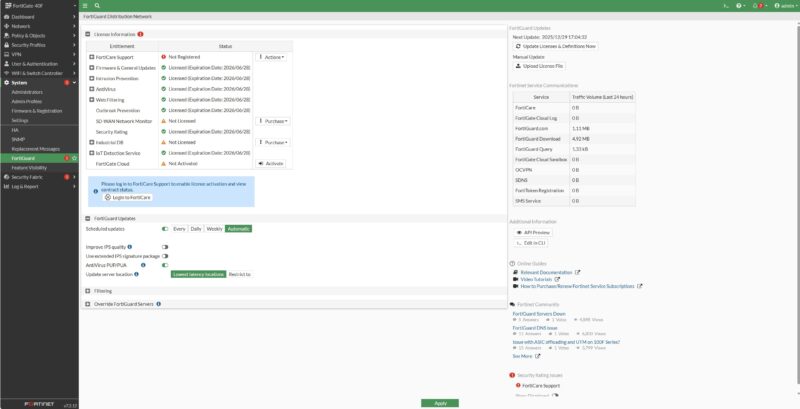
To do this review, we purchased the FG-40F-BDL-809-12 bundle. The FG-40F is the hardware. 12 is for the duration. The 809 means we have 1 Year FortiCare Premium and FortiGuard Enterprise Protection. These boxes have a ton of features and various license levels.
If you are coming from a pfSense, OPNsense, Ubiquiti firewall, or similar device, the entire licensing experience is jarring. It is something that you do not hear a lot about. There are people who regularly deploy these boxes and are accustomed to how this all works. If you are just entering the space, it is rough. For example, when you want to get your entitlements, you may think the flow is: username/password, name, e-mail address, verification, organization, address, and maybe a phone number. Critically, you need one more step, and that is to find a reseller.
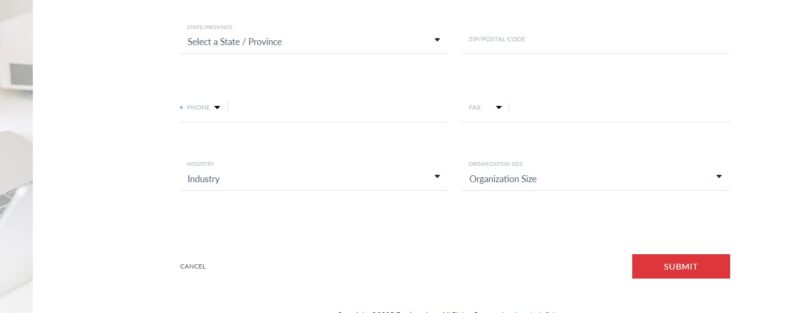
No matter if you are online or just trying to do several functions in the UI, you are also asked for things like the reseller name.
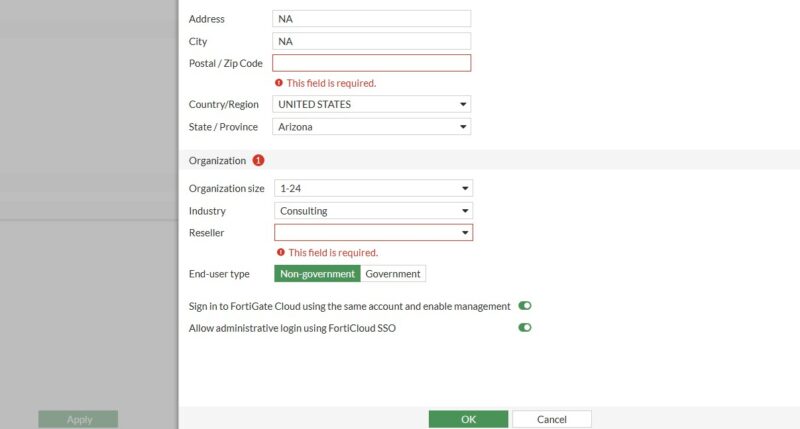
I totally understand this from back when I was at PwC doing consulting and building pricing, discounting, and deal management workflows for large tech companies. If you have ever worked on the sales side, this makes perfect sense. At the same time, things like the reseller we were asked for when adding future firewalls to the account.
We review servers, workstations, and so forth from every major vendor, and are covering a lot of the network switch space as well. We buy a lot of this gear. In the firewall market, this process seems common. Compared to the rest of the IT equipment market we deal with, this feels like a three sigma abrasive process. Again, I fully understand the desire and need to capture data like the reseller for a box to ensure channel partners are compensated. It is just a very noticeable high-friction process compared to others we deal with.
Next, let us get to the exciting bit.



I can’t wait for y’all to do more firewall reviews. Talk ’bout an opaque industry.
Any chance you will review the Watchguard Firebox M-Series (M270, M290) ?