Along with the 3rd Generation Intel Xeon Scalable Cooper Lake Launch yesterday and our Supermicro SYS-240P-TNRT 4P 3rd Gen Xeon Scalable Server Hands-on article/ video, there was another piece that we wanted to cover but did not have time to do so. Google shared a look in and around its data center by showcasing their 6-layers of security.
Layer 1: Signage and Fencing
This is one of those important aspects of security, but it is also probably the least exciting. Google posts signs and has fences around their data centers.
Conceptually the idea that Google would have signage and fencing around their facility makes intuitive sense. If you need to increase your layer count, this is a good place to start.
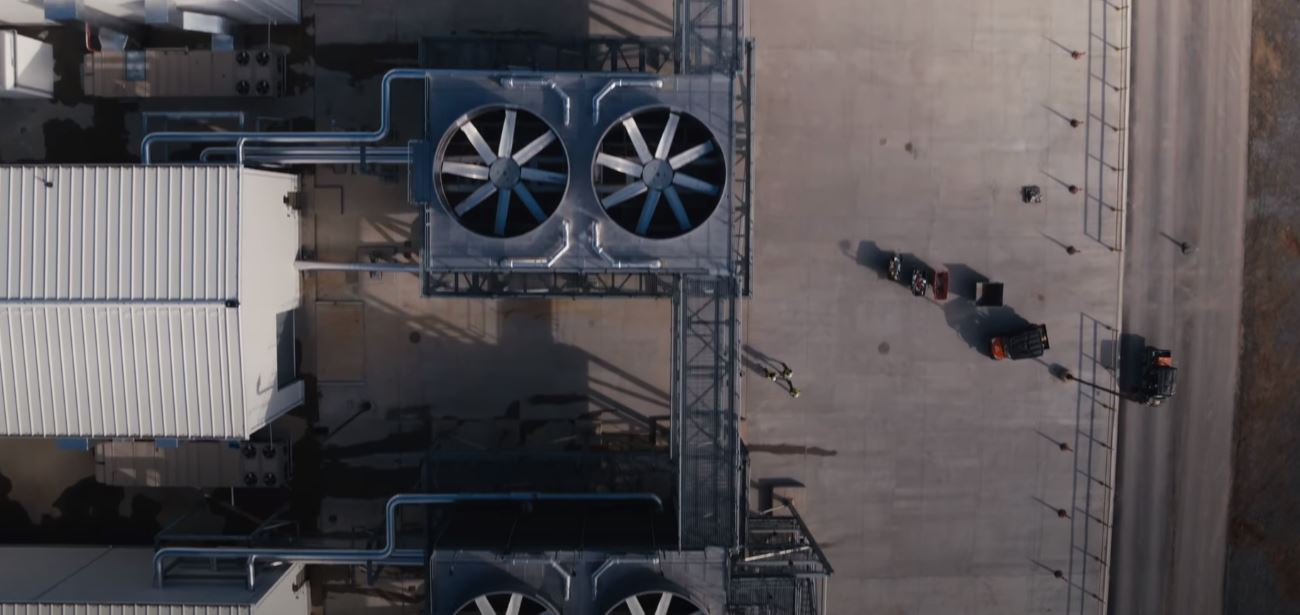
Layer 2: Secure Perimeter
In the secure perimeter, Google can see where you are via cameras including thermal cameras with overlapping fields of view around the facility. Google can track where a person has been in the facility as well.

Google uses an anti-climb fence, a guard checkpoint, and there is even a vehicle crash barrier designed to stop a fully loaded truck.
Layer 3: Building Access
Entering the building, not just the floor, requires that one is authorized. That includes going through a security checkpoint.
In the video, Google is using RFID badges, security personnel, and biometric (iris scanning) methods to validate the identity and access privileges of those trying to enter the exterior of the building. Inside the building, there are more security checkpoints before one can access increasingly sensitive areas.
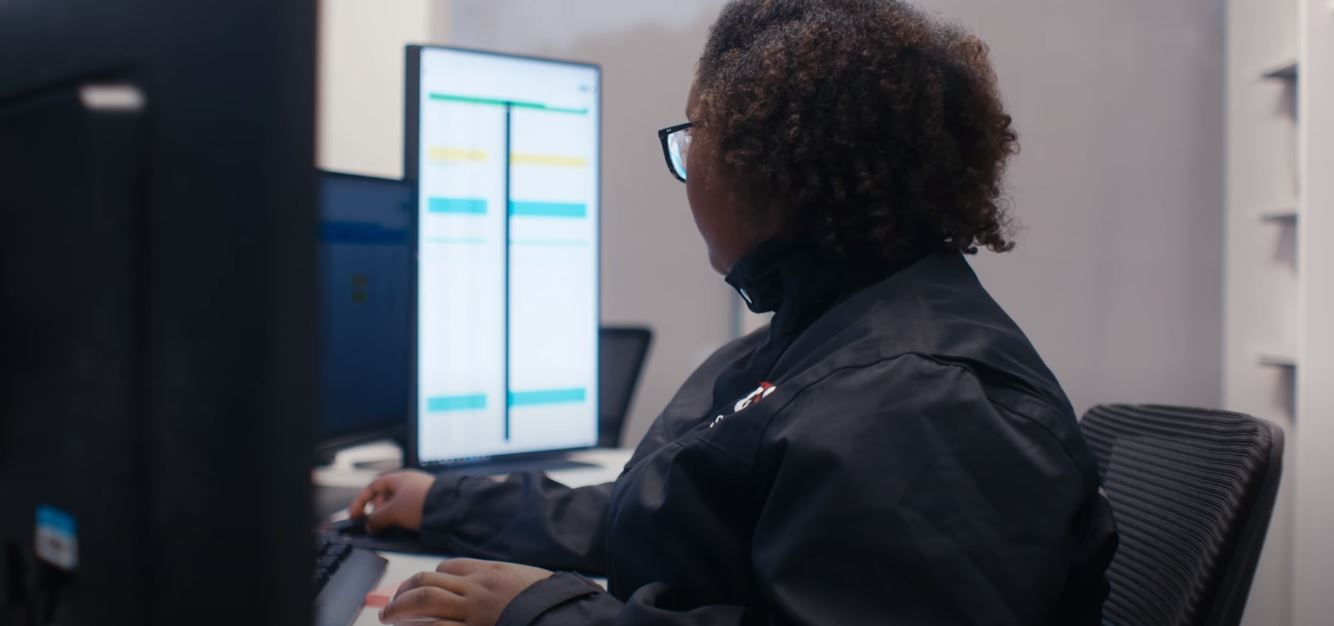
Layer 4: Security Operations Center
Layer 4 Google discusses its Security Operations Center and systems to monitor its data centers.

This is where the sensor and camera data are monitored. Google is showing a few of these and how they integrate with the security teams inside the facility and roaming the perimeter of the facility.
Layer 5: Data Center Floor
Data center floor access is limited to technicians and engineers that absolutely need access to that specific floor.

It is fairly typical for these facilities to have employees who have never set foot on the actual data center floor.
Google also notes that all data at rest is encrypted and that customers can bring their own encryption keys. As a result, those who have access to the physical machines do not have direct access to data that is on them.
Layer 6: Secure Hard Drive Destruction
Google facilities also have a secure hard drive destruction facility. Drives that are ready to be destroyed are passed to the destruction room via a two-way locker. That way, only authorized personnel in the drive shredding room will have access to the drives.

For those wondering what prevents someone from walking out with drives aside from cameras, there are features such as security and metal detectors for leaving the Google data center so someone does not remove hardware without authorization.

Here is the video which is worth a watch:
Final Words
From what we have heard via industry sources, Google’s setup is similar to what Amazon AWS uses. AWS is usually more tight-lipped on their data center operations but the concepts seem to be the same.
Compared to the average colocation or enterprise data center, these are more secure facilities. While there are some facilities that prioritize security, the large single-tenant facilities help Google run an efficient operation. That means they do not have to make the same trade-offs for hosting multiple customers as shared facilities.

It was also great to see some of the hardware Google uses since Google is more secretive than OCP members such as Facebook and Microsoft.
Just to give one a sense of the scale of what Google has seen, via Google’s SFP of technical infrastructure Urs Hölzle:
https://twitter.com/uhoelzle/status/1273670254363725833




Love watching these kind of videos. Similar to your Inspur adventure.
Hopefully AMD will bring out a new(HQ) version of this video from GF:
https://www.youtube.com/watch?v=qLGAoGhoOhU
Their “How a ZEN core is made” video was too short.
Just another Google DC airview:
https://www.google.de/maps/place/Green+Box+Computing/@53.4245004,6.8613746,809m/data=!3m1!1e3!4m5!3m4!1s0x47b627638c513eeb:0xe6afaad6673324a9!8m2!3d53.4258201!4d6.864249
https://www.openstreetmap.org/#map=16/53.4244/6.8634
mr robot dont like this :D :D :D
Wicked cool
It’s almost like home :)
Once had a tour in the Datacenter for the Frankfurt Stock Exchange, wasn’t to bad either.