Speculative execution is a technology that has undoubtedly played an enormous part in processor advancement over the past few decades. Spectre and Meltdown showed how these can be dangerous as clever code can exploit speculative execution. As the industry has patched for Spectre and Meltdown, we now have Foreshadow which targets Intel secure enclaves (SGX), virtual machines, and hyper-threading through L1 Terminal Fault attack (L1TF.) These speculative execution exploits are difficult to understand so we are going to try distilling everything down to the key points.
Foreshadow L1 Terminal Fault Attack
The Foreshadow L1 Terminal Fault Attack is another attack that is difficult to visualize. So all of our readers can share what L1TF stands for. L1 is the low-level processor cache. In Intel architectures, a “terminal fault” is what happens when a speculative page table lookup fails. Armed with that vernacular, the essence of the attack is that a malicious actor can exploit how Intel CPUs do L1 cache page table lookups to gain access to information that they should not have access to.
Largely left out of the Spectre and Meltdown discussion was Intel SGX. Intel SGX creates a secure enclave to store sensitive information that even an operating system is not supposed to see. With Foreshadow, researchers have been able to peek inside SGX and get to extremely sensitive data. If you want to see this in action, there is now a video of the attack available:
Modern CPUs utilize simultaneous multithreading or SMT. On Intel CPUs vulnerable to Foreshadow, the feature is called Hyper-Threading. Hyper-Threading on the mainstream server and desktop CPUs allows two threads to be executed simultaneously on the same execution core. In our reviews, we call this out when we say, for example, the Intel Xeon Gold 6134 has 8 cores and 16 threads.
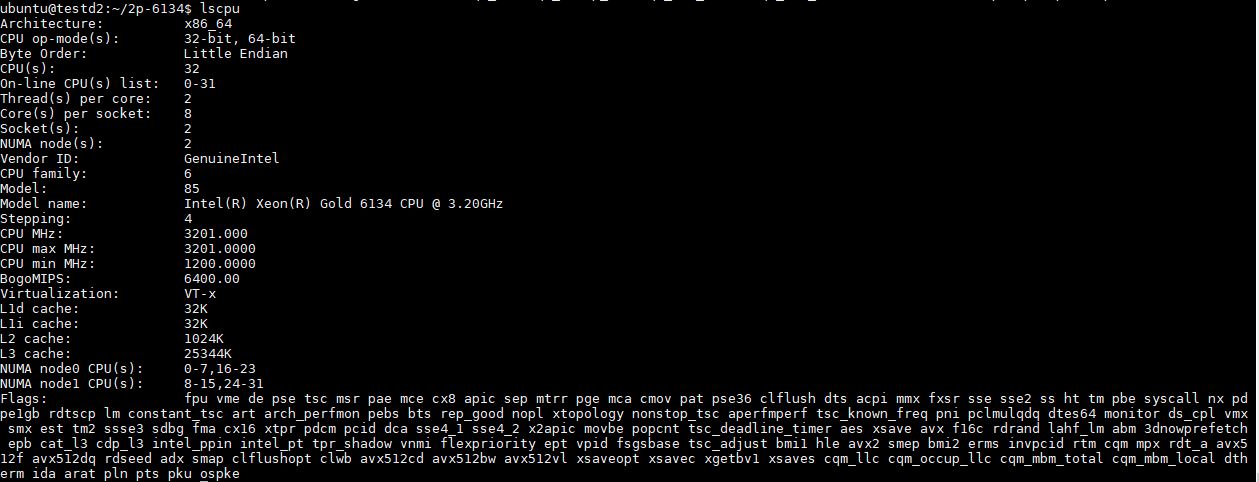
Part of Hyper-Threading’s “magic” is that chip designers realized that portions of the core, especially caches, can be utilized by more than one thread. Adding Hyper-Threading is a relatively small overhead compared to adding a physical core making it a great performance benefit. While there are a few use cases where Intel Hyper-Threading is turned off (e.g. some HPC applications), in most cases modern CPUs gain a massive benefit that we often approximate as 30% performance boost from the feature.
Due to the fact that both threads on an Intel Hyper-Threading core are executing using the same cache resources, this mainstay of enhancing performance also means that there is a shared level 1 cache. On the desktop side, this is less of an issue since OS vendors can patch the OS and most desktop users are not running untrusted virtual machine code on their systems.
Where this gets slightly scarier is with Intel virtual machines. If a bad actor creates a corrupt extended page table in their virtual machine, they can trick the hypervisor. The hypervisor can then reveal information to other virtual machines. Hyper-Threading in the multi-tenant cloud means that VMs from two different users can be running on the same physical core as two threads. One VM can use L1TF to then try gaining information about the other. This is a big deal for cloud providers since the cloud is multi-tenant native. For enterprises that have virtualization clusters or private clouds running untrusted VMs, this can be equally concerning.
Foreshadow Mitigation
This vulnerability was disclosed to Intel and other parties months ago. In the meantime, patches have been released. Those that we have spoken to say that the performance impact for bare metal servers is negligible.
In virtualized multi-tenant systems there is a major implication. Although there is a L1 cache flush patch available for hypervisors, it also means that a major mitigation step is to turn off Intel Hyper-Threading. We regularly see a 30% improvement on many of our workloads in the STH lab with Hyper-Threading so turning off the feature can have an enormous negative impact on performance.
Where to Learn More
The Intel site for L1 Terminal Fault / CVE-2018-3615 , CVE-2018-3620,CVE-2018-3646 / INTEL-SA-00161 is here.
Check out Red Hat’s great write-up of the attack. They also have a video that explains everything at a higher level that you can see below:
Redhat even has a more technical video online:
Here is the official video from the official website:
Also, this may sound Intel focused, but AMD confirmed their chips are safe including their implementation of SMT. See here.