In 2001, Hugh Jackman was cracking 128-bit encryption for John Travolta and Halle Berry in the movie Swordfish. Over the next 15 years, computers have gotten a lot faster. We decided to take the 2.7kW Supermicro 8x GPU server STH reviewed last year and see if we can do a bit of cracking of our own.
In the movie, Hugh Jackman’s character, Stanley, is asked to crack a password prompt protected via 128-bit encryption.

The movie had (then) state-of-the-art equipment such as a workstation with seven monitors (LCDs even!) In the fifteen years since the movie was released, we have seen trends towards monitors aligned in a more organized fashion.

The DS3 (45Mbps) connection? Insane speeds then, but now is not that much faster than cellular wireless data speeds in some geographies. This was well before we had hardware encryption on processors making encryption on modern hardware essentially “free”. In 2001 we saw the release of 1.3GHz Pentium 4 chips. These single core processors were about 1/100th the speed of today’s desktop chips. Also, GPU compute has been a major trend which has taken some tasks like crypto hash acceleration to a new level.
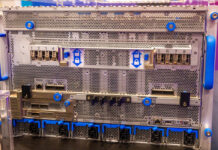
Without either Halle Berry or Helga (Laura Lane) peering over our… shoulder, we decided to use oclHashcat to crack a MD5 password hash. We used this version so that we could use our 8x AMD FirePro S9150 GPU compute cards in the Supermicro SYS-4028GR-TR server.

So what happens when you pit MD5 era encryption against a ~$30,000 4U server from 2015-2016? Suffice to say, the result was shocking.
We picked a relatively short password for that era. The leading edge of the millennial generation and those older probably remember the days when you could use passwords like “pass” “user123” or your name like “patrick”. Even into the early 2000s 8-character or longer passwords were not standard. There were infrequently requirements for uppercase letters or numbers. For our video we used the password “swfish12” and translated that into an MD5 hash. Our objective was simple: see how long it would take our server to crack the MD5 hash and get back to “swfish12”.
We went to a local coffee shop and saw what we could do with a laptop and the 8x AMD S9150 system remotely tucked away in the DemoEval lab.
After logging in remotely this is what happened:
Not only did the server crack the password, it did so in less time than it takes to drink a cup of coffee. The actual compute operation had a timeline much closer to a sip of coffee.
Here are a few takeaways from this exercise:
- If you are using short passwords with low complexity, change them.
- We took a matter of minutes to go from zero to this crack. This was not the effort of a security researcher and instead one of a non-expert taking 20 minutes to read a FAQ on the Internet and setting the system up. We even left Windows on the machine (it was needed for a certain GPU rendering package we were testing.)
- If this machine was in the hands of a skilled security researcher, the MD5 password would have taken under a second of execution time instead of the 9 seconds it took us.
- If you have a critical application from the 1990’s or early 2000’s running, it may be worth paying an expert (not us) to do a security audit.
- There is almost always work involved to get to the MD5 hash which we did not show. Passwords are stored today with stronger hashes to prevent these speedy attacks and getting to them is often difficult.


But can your fancy $30,000 server crack the security around Halle Berry’s repositories? Answer me that!
Might have been a bit more impressive with a 9 character random ascii character password.
But truthfully weak passwords make most password files a fairly weak form of security.
Pushing the length up to 9+ characters and using characters that you can create a mnemonic for are generally still strong but I don’t see the human factor being resolved any time soon. Like the locks on your door at home they really don’t provide a significant amount of security. You can pick the lock, kick down the door, break the window, go through the wall or simply wait until someone opens the door for you.
Anonymity and Privacy are becoming abstract concepts on many levels. With our new found computational power and disk space we now have the ability to sift through the endless streams of crap and turn it into value both good and bad.
There’s probably a meme for this.
Hilarious, great article. Swordfish has been my goto joke for stupid Hollywood hacking depictions. The 7 monitors spread out in a circle get me every time.
5/7 would donate another server to see the results!
Please try a similar test with AES 128 bit hash?
Zia – we do not have the server anymore. Will try with the next GPU compute server we get.
Was the md5 at least salted? I wonder what the operating systems of those days used….
Salting won’t change the output of a brute-force attack, which this was. It can help with dictionary and rainbow table attacks though.
The recommendation and usual practice to use passwords of 8 characters or less could’ve been due to a constraint on early Windows versions: Those stored for every 8 characters a new (and independent!) password representation. Sysadmins therefore recommended passwords with multiples of 8 chars – and obviously very few individuals have been inclined to go for a 16-char one when one with 8 chars sufficed.