A few months ago, we covered a new offering from HPE called its Trusted Supply Chain Servers. These are servers that have a country of origin USA, but in the future, the company plans to roll-out to other countries and regions. After that discussion, HPE sent a server to check out the new offering. The server itself was a step up from a barebones configuration with a single Intel Xeon Bronze 3204, 8GB of memory, and a 480GB SSD. Instead of reviewing the server as we would a more standard offering, we decided to take a look specifically at what the server offers. Of course, since this is STH we also tore the system down to see where the parts came from.
HPE Trusted Supply Chain Background
First, we wanted to discuss the HPE Trusted Supply Chain. Let us start, that this is an offering that makes immediate sense. All major global governments and critical sectors are looking for a way to secure the building blocks of their technology infrastructure. We wanted to take a look at the hardware behind the offering. For those that prefer another format, we also have a video going through this offering:
As always, we suggest opening the video version in a YouTube tab since that offers a better viewing experience. Feel free to listen along as you go through the rest of this article.
In 2018 there was infamous Bloomberg article has seen its major sources say that the article was incorrect, including Supermicro, Apple, and AWS (see Investigating Implausible Bloomberg Supermicro Stories.) The publication’s follow-up piece to bolster its case after questions were raised focused on a security researcher, Yossi Appleboum. STH was able to interview Mr. Appleboum who said this when he felt his comments about supply chain security were published by Bloomberg, “I am angry and I am nervous and I hate what happened to the story.” While the original story seems to have parties involved saying the story was inaccurate, it raised the question of hardware security in the industry to a level it had not been previously set at.
One of the key issues raised was how IT equipment passes through many hands both through the manufacturing process, but then, and perhaps more poignantly, between the manufacturer’s shipping dock and the customer data center rack. Each touch invites the potential for tampering. As a result, the supply chain around physical access is a weak link. These days, we see major hardware players both as cloud providers as well as enterprise servers and even consumer devices looking to ensure that devices are not tampered with through the supply chain.
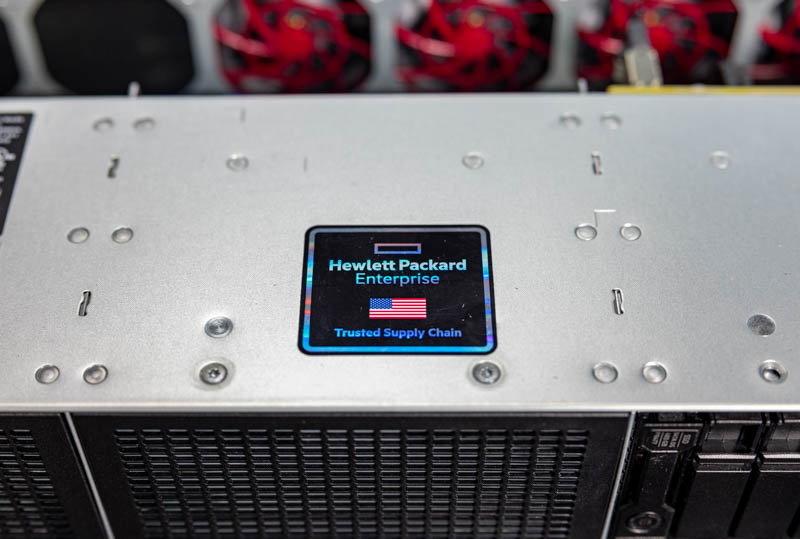
This is exactly the challenge that the HPE Trusted Supply Chain is trying to address. Against that background, we have HPE’s first Trusted Supply Chain offering, the HPE ProLiant DL380T. That “T” stands for “Trusted”.
HPE ProLiant DL380T Gen10 Trusted Supply Chain
HPE is effectively making a higher-security supply chain for some of the US Federal, financial services, and critical infrastructure spaces. The main goal is to ensure that the server that leaves HPE’s shipping dock arrives undisturbed to its customer’s racks.
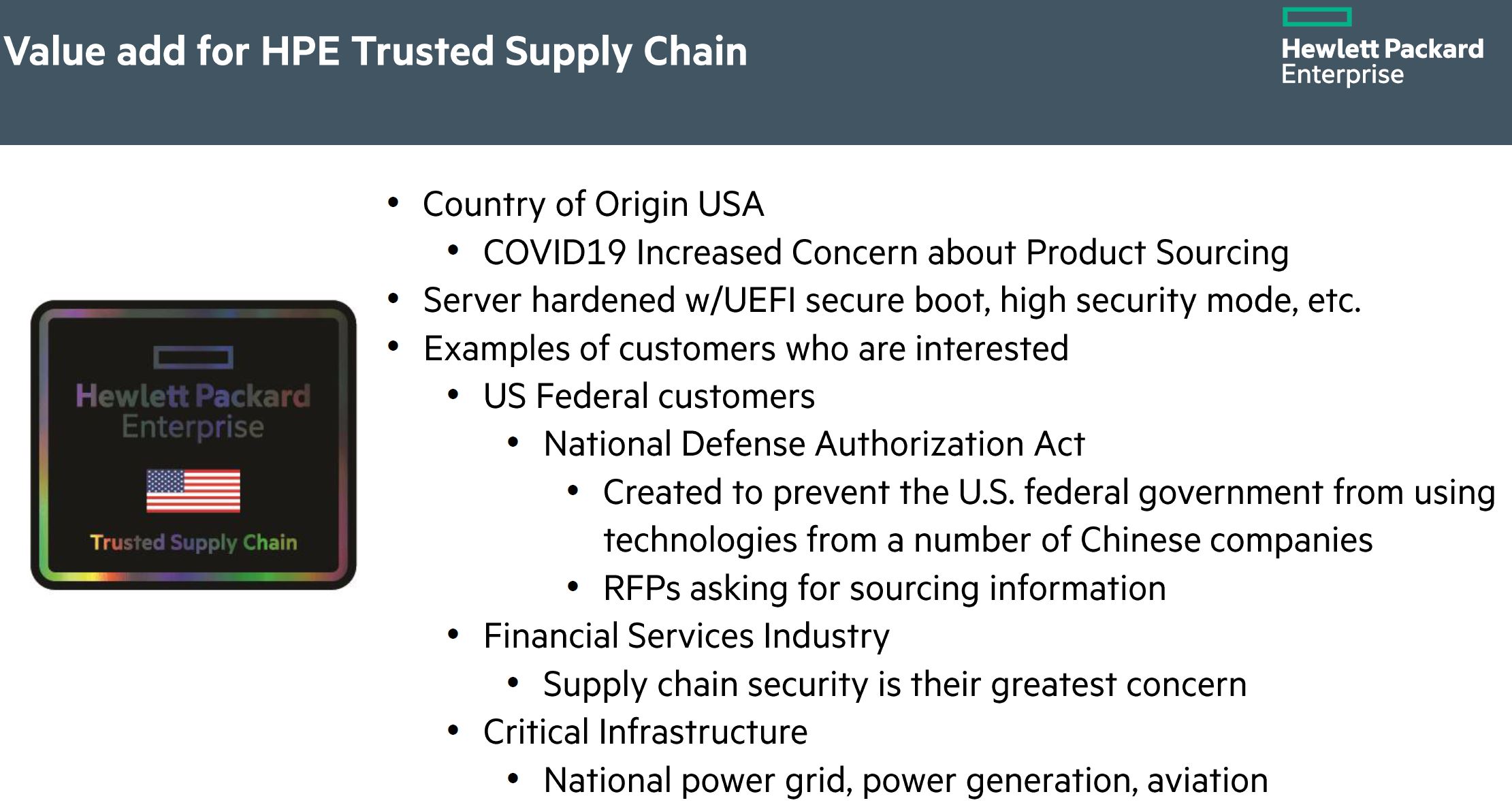
HPE has a manufacturing facility in Chippewa Falls Wisconsin. There, it has vetted personnel that can assemble the server. We also asked HPE, and they said they have met the requirements for getting a Country of Origin USA label. Note, that is different than the Made in the USA program. When we did our first piece, we were told not all of the components are manufactured in the US, but enough are to meet requirements. We are going to look at that in our teardown.
Key here though is that Country of Origin does not mean that all of the parts do not need to be from the US. Instead, it is more of a substantial transformation test. From the CBP website:
The country of origin of an article may be changed in a secondary country if one of the following occurs:
- If the further work or material added to an article in the second country constitutes a substantial transformation. A substantial transformation occurs if a new article with a different name, character, and use is created…” (Source: CBP.gov accessed 2021-01-19)
We are not going into all of the details here, but “substantial transformation” in this case seems to be the server itself. Again, HPE told us that it met the requirements for Country of Origin, and so as we tear the system down, this test is important to keep in mind because otherwise, one may misinterpret what the label “Made in US (Includes Foreign Content)” means.
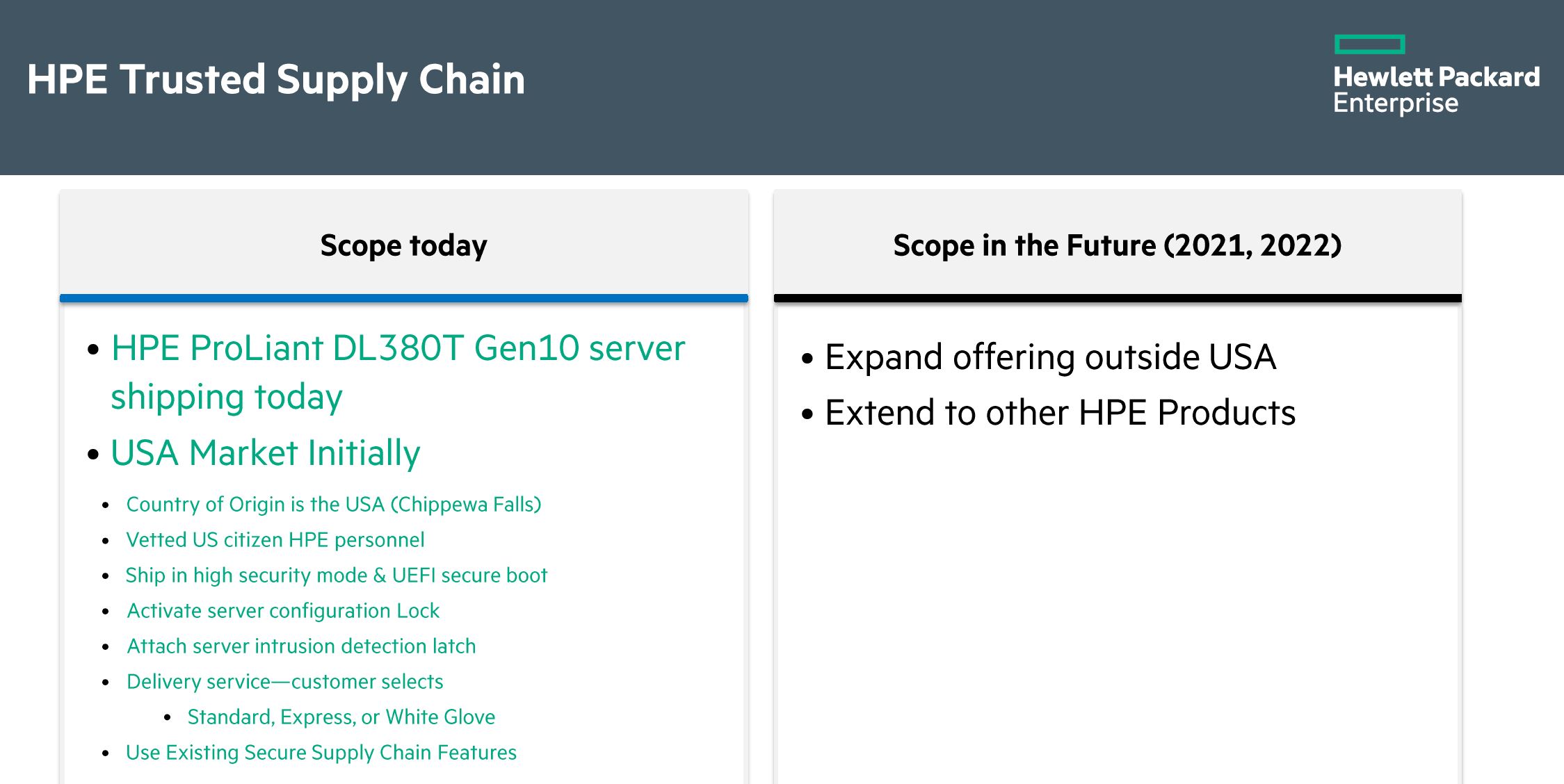
HPE has a server configuration lock feature that uses cryptographic signing to ensure that the configuration that leaves the factory is the same configuration that is next booted. If a component is altered or swapped, that is immediately flagged so that operators know a change has occurred. One also has a key that HPE sends to unlock the server once it arrives. This is important for ensuring configurations remain safe after they leave the factory.
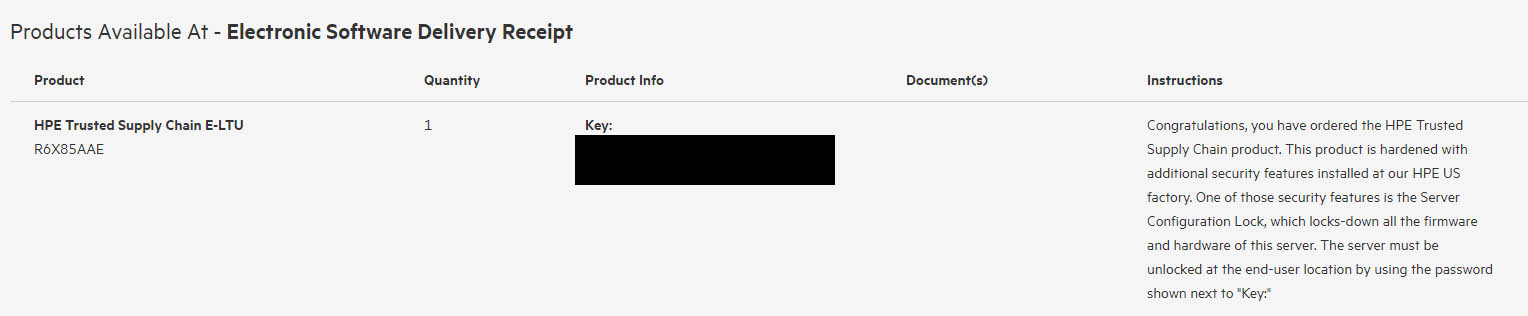
Keeping hardware shipments safe after they leave the factory is a major industry concern. Interception of servers in-transit is a big deal since they can often pass through logistics chains that can be compromised. Not only does HPE offer a secure firmware base, and the ability to configuration lock the systems, it can also deliver the servers to data centers and get them installed. This allows HPE to screen the folks in the logistics chain handling servers adding another layer of security.
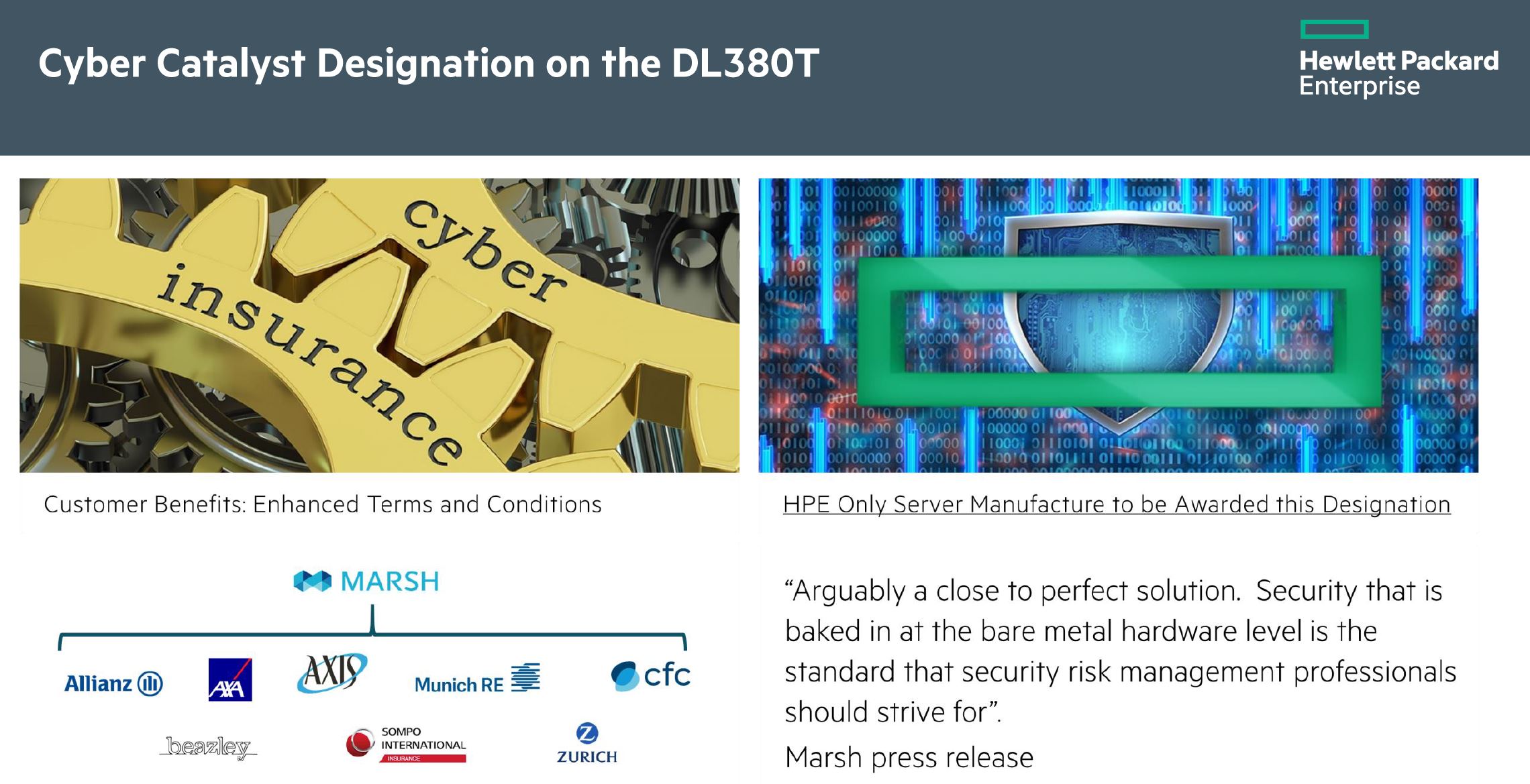
The cost of the “T” series servers is higher, but it is not expected to be a 50-100% premium. Our sense is that the market will likely pay a 10-25% premium for this designation. Part of that cost will be offset by what HPE says is a lower cyber insurance premium.
Overall, the aspect to keep in mind here is that the server is built and configured in the US where HPE can validate that the components and system meet specs. It implements safeguards to help ensure that the server was not tampered with in transit and arrange the transportation logistics to help provide more security. The bottom line comes down to making sure servers do not pass through windows where they are vulnerable to physical tampering.

Next, we are going to get to the hardware since we wanted to see how much of the hardware was made in the US.





I don’t care about the metal and plastic. I do care about the drives, memory, processors, chips, PCBs, and other electronic parts like wires and fans. You went too far in the teardown.
Well this is very nice and all but let us have a conversation about BGP highjacking if we are all worried about what the funny chips that the evil forners put in our servers do.
@RunsackAL, while some have nationalist concerns about the origin of their products down to the smallest details, I would agree that an article addressing “Trusted Supply Chain” could probably ignore case “metal and plastic” parts (including PCB board).
So server comes from trusted supply chain and pcb is made in China? Is that a joke or two? Or has HPE really put the pcb under microscope and verified everything to the latest detail? Can’t believe this at all…
Patrick, in negativity against HPE put into previous comment I’ve forgotten to thank you for this wonderful article. That’s something I’ve been diging into recent months and it’s indeed highly complex task to get some meaning full information about the components country of origin from the hardware vendors. Servers are in the first battle line so I would expect way better job performed by HPE here, but the hell I got with notebooks is unbelievable too. Vendors freely claim that their notebooks are assembled in U.S.A. while it’s clear that this is ODM work done somewhere in China or in the best case in Taiwan etc. etc.
It’s really hard to source some components which has not been on mainland China…
I’d really appreciate if you would just enhance your future articles by single line or two mentioning also component/system country of origin. Would help a lot here. Thanks for all your great work!
Wowza. Thank you for doing this. This is a great level of detail.
US-made is the opposite of trust.
Looks like assembled in the US with some papers printed in the US. Once assembled, all transport is domestic which makes supply chain interruptions harder. Over time I wonder if they will start utilizing more North American supply sources for more of the platforms.
See the FTC website: https://www.ftc.gov/tips-advice/business-center/guidance/complying-made-usa-standard#Assembled%20in%20U.S.A.
Assembled in the USA.
I’m not going to pick on anywhere in this comment, but I wouldn’t want to pay extra for this configuration; I’d prefer to source my own motherboard.
Trusted Supply China