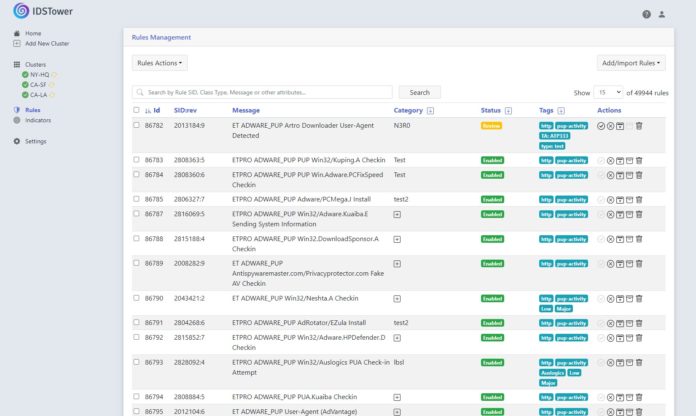
This week saw a big release in the network analysis and threat detection security space with the release of Suricata 7. This is the first major version release since Q4 2020. For STH readers, many are using intrusion detection and prevention systems (IDS/IPS) based on Suricata in environments like pfSense and OPNsense as well as others. Since Suricata does not have a GUI, and we like cover images, the cover image here is from a IDSTower environment which is a popular GUI for Suricata.
Suricata 7 Released First Major Version Update Since 2020
Suricata 7 brings a host of new features. Some of the big ones are:
- DPDK IDS/IPS support for primary mode was added
- AF_XDP IDS support by Richard McConnell at Rapid7
- HTTP/HTTP2 new keywords for header inspection
- TLS: client certificate logging and detection
- Bittorrent parser by Aaron Bungay
- IPS: new default DROP behavior for exception policies
- EVE documented and validated with a json schema
- HTTP/2 support is no longer considered experimental
- NETMAP API 14
- Conditional PCAP by Eric Leblond and Scott Jordan
- Initial libsuricata support
- VLAN support extended from 2 to 3 layers (Source: Suricata)
Many of those updates are features that the community has wanted for some time so it is great to see them added. Now that Suricata 7 is out, we expect packages that use the new version to start making appearances. For example, we checked pfSense 2.7.0 CE this morning before publishing and it was still using Suricata 6.
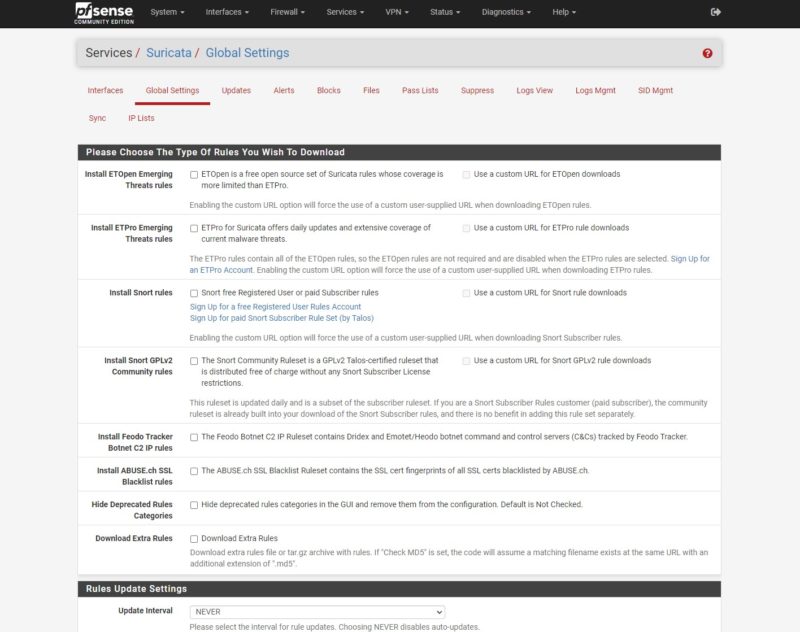
Usually, it takes a bit of time for the new versions of tools like Suricata to be updated in projects, especially when there is a GUI component.
Final Words
We purposefully waited to post this until Saturday since we know that a set of our users utilize Suricata and this new release will send them into testing Suricata 7 over the weekend. For the popular IDS/ IPS project, this is a major milestone with the new version. This is one where we should cover the project more on STH, and so we wanted to at least cover it briefly here.