In August 2015 we published our hardware review of the pfSense SG-4860. As with many network appliances, first impressions are great, but what about longer term stability. Today we have our impressions of the unit with over 6 months clocked on it.
The Big Question: Stability
Admittedly, when I saw that the pfSense SG-4860 did not include an active cooling solution I was at least a bit concerned about the stability of the unit, especially since I had the unit at home and our house can get warm in California summers when we are away. I am pleased to report we have had a total of two reboots of the unit in over 7 months. Those two reboots were solely due to upgrading to latest security releases. Here is a current snapshot showing 83+ days of uptime.
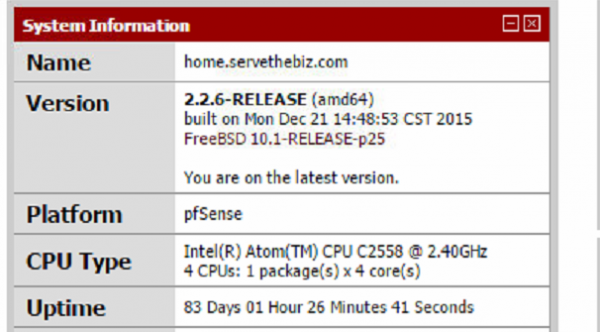
We upgraded to pfSense 2.2.6 after it was released on December 21, 2015 and the unit has not flinched since then. When it comes to stability, the pfSense SG-4860 is excellent. Total reboot time is measured in seconds so scheduling downtime for upgrades has not been an issue.
VPN Performance
We use OpenVPN tunnels to both our Fremont, CA and Las Vegas, NV datacenters. These tunnels are able to push line rate speeds of 100mbps to both datacenters simultaneously without issue, and will even support a third to our Sunnyvale, CA pfSense firewall. Furthermore, the tunnels generally stay up for at least 30 days straight. We have seen the OpenVPN tunnels reset, but the connection gets re-established within seconds and have yet to see the replication jobs we have running fail due to the OpenVPN resets. There is likely a way to squeeze more uptime from the tunnels but since the only way we even can tell they were reset is from the status page, this is not something we have seen value in working on.
Understanding Rangeley Impact
Intel is working with STH on doing a formal QuickAssist Technology (QAT) piece but the Intel Atom C2558 onboard our pfSense SG-4860 review unit has the QuickAssist engine built-in. QuickAssist, from Intel’s press briefings is something that is going to greatly increase VPN and compression throughput in the future and we have heard the pfSense team is putting work into supporting QAT. Even with lower power consumption and instructions-per-clock performance than newer chips like the Xeon D line Juniper is using in their NFX250 appliance, the SG-4860’s onboard Atom C2558 is still going to deliver better performance per watt.
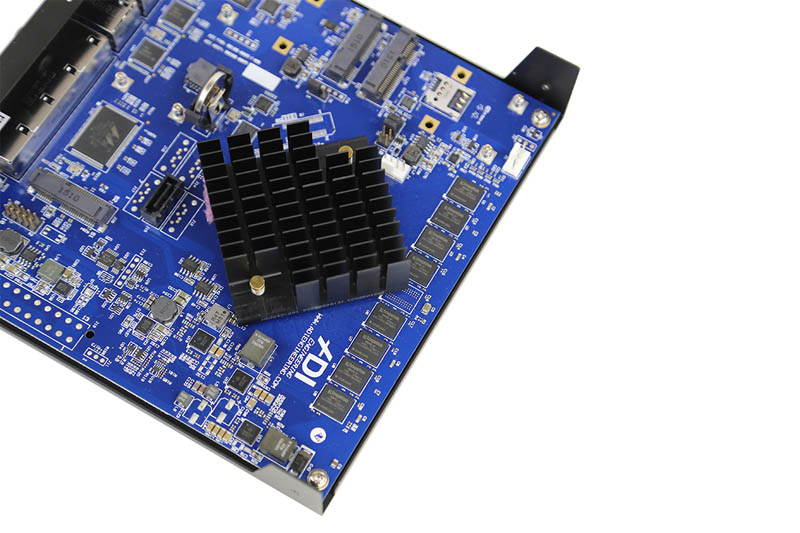
While the Intel Rangeley CPU has performance upside in the form of QAT, The average prosumer or SOHO router/ firewall solution does not. This was a great choice of CPU for the pfSense team and ADI Engineering team who collaborated on the hardware.
pfSense Software Packages
One of the other great items we see with pfSense is the ability to use their package manager. The package manager provides a GUI for installing additional functionality as well as updating packages. Unlike several years ago, there are now packages for just about every network service on might want to run. Here is a screenshot of just a few lines in the package manager:
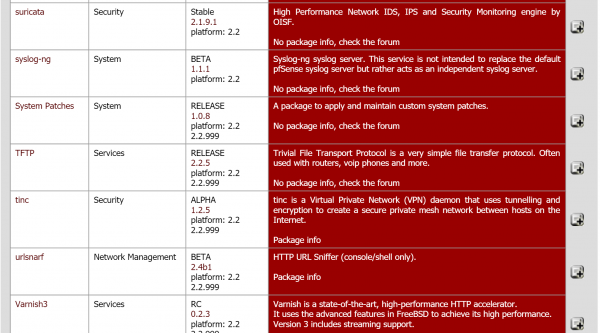
One can see suricata IDS/ IPS engine as an option. One can also see services such as the TFTP service (useful for updating embedded firmware for example) and even web services such as Varnish3. We recently did a short how-to article on setting up pfSense and HAProxy load balancer. The pfSense package manager certainly made that task very simple. There is a short description (red column) next to each package so even a novice admin can search on the page for what they might need. Suricata is certainly an awesome package that runs well on the pfSense SG-4860 hardware.
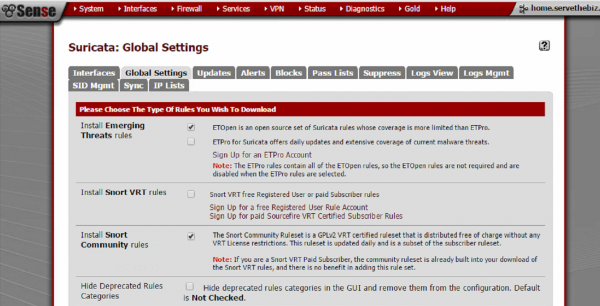
If you want to read more about suricata, please check this page. pfSense has a WebGUI to assist in configuring the solution which certainly brings down the overall experience level required to get this up and running. From a home standpoint, suricata was installed months ago and my wife has still not noticed any ill effects.
pfSense SG-4860 – 6 months in – how good is it?
After 6 months of utilizing the pfSense SG-4860 on a daily basis, and pfSense elsewhere in the STH architecture, it is great. Primary requirements for a SOHO appliance are the ability to:
- Secure the facility from unwanted traffic
- Utilize the entire LAN/ WAN bandwidth
- Install network services/ rules to meet expanding use cases
- Provide VPN access to remote locations
- Be stable!
On all counts the pfSense SG-4860 has performed very well over the past six months. For those struggling with inexpensive SOHO routers where stability is, at best, questionable at times, there is a major benefit in upgrading to a more powerful unit like the pfSense SG-4860. Even though at STH we have a choice of using just about any piece of SOHO, SMB or enterprise equipment, we are still using the pfSense SG-4860 because it has been absolutely great. Suffice to say, we are eagerly awaiting the pfSense 2.3 release and getting to try the SG-4860 on the updated software.





Have you had a chance to speed test the device? For those of us who are lucky enough to have Gbps internet, we want to try to maximize throughput and as soon as you turn on IDS/IPS, regardless of the device, speeds drop to around 300-400 Mbps.
I running this unit using AT&T’s GigaPower – Gbps internet. I can easily reach full bandwidth – up and down in the low 900s.
And the speed with AES-256-CBC encrypted VPN? I’m looking for a router that can handle 250/100Mbps as a VPN Client.
How much ram is consumed running PFSense with Suricata in your setting?