At STH, we are now in our eighth year of reviewing tech. As a result we have experienced many cycles of technological leaps and incremental refreshes. A lot of what we cover is focused on incremental changes. Some days there are leaps that make you smile. The Netgate SG-1000 is one of those leaps. We are going to have our full review coming once we get more time under our belt and as pfSense 2.4-Release becomes live. At the same time, this is a device that 12 hours into using it evokes a smile each time you look at the form factor because you can think of a new use case. We are also testing the Netgate SG-1000 with the popular FreeBSD firewall appliance software, pfSense (2.4-beta). We expect pfSense 2.4 will be the milestone where ARM-based pfSense appliances will become more popular.
First Look at the Netgate SG-1000 with pfSense
We are going to save the teardown pictures for the full review, as well as looking at accessories like the wall mount kit. In this piece, we simply wanted to show what the solution looks like. The unit Netgate sent was bright red, but there is an understated black available. I am fairly certain someone will 3D print cases like STH community members did with the Raspberry Pi.

To give a sense of scale we looked around the lab for common items. We had a SanDisk Lightning Ascend Gen II drive nearby which is a 2.5″ SAS SSD. That should help with dimensions as well as the WAN and LAN RJ-45 ports.
On the opposing side there are console and USB OTG ports. The serial console cable is USB based while the USB OTG adapter is an inexpensive add-on. There is a power LED as well as a power input port. This unit is relatively simplistic.

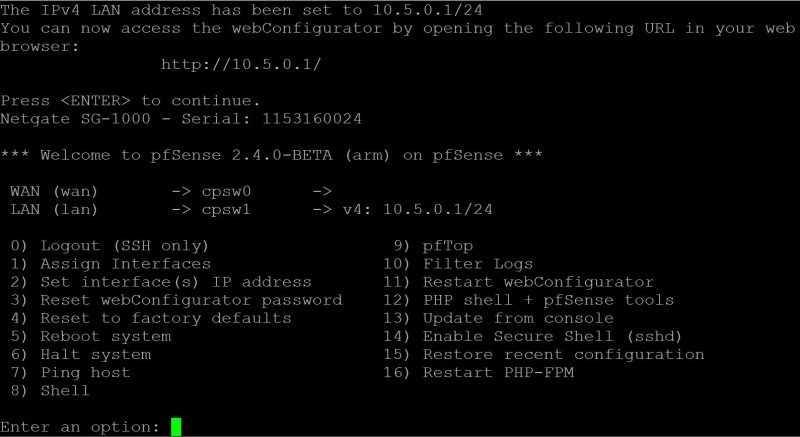
Our unit came pre-installed with pfSense 2.4.0-BETA for ARM.
Using the included USB serial console we saw COM3 on our laptop. By the time we could open a serial Putty session at a 115200 baud rate, the unit booted and we could easily access the CLI.
In terms of the web UI, you can see that the responsive UI from pfSense.
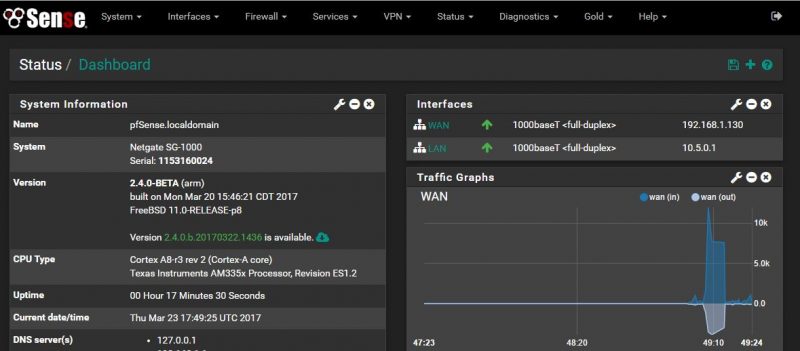
Unique to the Netgate SG-1000 we see CPU Type listed as a Texas Instruments AM335x ARM Cortex A8 CPU.
To answer the first question we are likely to get, we still need to run load testing. Thus far the highest peak is well under 5W and closer to 3.4w shaving a few tenths at idle.
Another Perspective
If you are a pfSense user, and have not subscribed to pfSense Gold ($99/ year), the SG-1000 needs to be on your shopping list. Likewise, if you are thinking about deploying a higher-end pfSense appliance, get this first. For $149 you get a 1-year pfSense Gold subscription. You can read about our pfSense Gold Subscription: Initial Impressions when we tried it out in 2015 and that was after having used pfSense for years and more content has been added since.
From initial impressions, if you need a 1GbE pfSense firewall with many features turned on while still operating at or near line speed, we are not going to recommend the SG-1000. On the other hand, if you just want to learn pfSense or need an out of band management VPN gateway, this is just about the perfect device. If you want to get your friends and family on pfSense plus separate AP’s, the pricing on this unit is approaching high-end home market levels.





The problem with that product is that’s missing the 3rd network card. where you could put the DMZ or another network e.g if you have a IP range that goes to the servers + additional ip that goes to the workstations..
If you truly need a 3rd network, and are running servers you should have the skills necessary to set up a managed switch and vlans… I’ve never understood the point of having tons of physical ports on a firewall appliance.
One of the issues with VLANs is that the physical interface bandwidth is shared, so if someone had the skills for setting up servers and such, (s)he might also want LAN DMZ bandwidth to be maximized.
True, but it’s highly unlikely that someone needing gigabit wire speeds on multiple different networks is going to be shopping a $149 ARM based device.
I fully agree that a third NIC would be an interesting product. Then again, there are a number of different pfSense platforms that they sell or that you can buy that are more capable.
My intent with the full review is to put this into context for a product that is very small (it is smaller than my ODROID and Raspberry Pi 3 boards), uses <5w of power and therefore can provide firewall/ VPN services. I think, for example, if you have a DMZ with 5 devices, a non-DMZ LAN with 30 devices, a VPN-only management LAN, a vlan for wireless clients and another for wireless guest clients, then spending a few dollars more on a higher-end system with an appropriate feature set is worthwhile.
Looks like a good entry level device to get your “feet wet” with psfense, a usable training aid. The concept is sound and the price point is good.
I ordered one yesterday to play with; I just wish this and the other Raspberry Pi and clones would run over PoE out of the box…
So I also have to buy a managed switch which costs more. Instead of having something simple as running a couple of VMs test services that are but rarely accessed from the outside. Also the link is 100/20 so…
It would be interesting to see how it compares to the $55 mikrotik hEX gr3: https://routerboard.com/RB750Gr3
That hEX Gr3 supports IPSEC hardware accel and can push encrypted tunnels around 550Mbps.
Are you thinking this one? I just ordered so we can check it out.
That is not an issue in a device such as this. The WAN port is 1 gbit, the lan port is 1 gbit – you won’t route LAN data on this device and you won’t have traffic originating / ending up at the router either (basically just the web interface – thus negligible).
So that VLANS share the same bandwidth is a non-issue for the use-cases intended for such a device.
Echo, but you would route lan data with the device that way you can inspect and enforce compliance with rules created in the firewall. If you wanted to push the routing off to the managed switch, then you just buy a managed switch smart enough to do NAT, and you send the Netgate back for a refund.
At the price point it’s at, it’s perfect.
I’d be very interested to know how well alternative OS’s run on it like a pure BSD or Linux dist.
dougsk:
Um, that seems quite esoteric?
And if that is what you wanted just mirror the port in the switch instead? Or relay it through some other device, because if that’s really your scenario surely you wouldn’t trust pfsense to route the traffic if pfsense is the device you want to validate?
Regardless this device isn’t nearly capable to sustain 1 gbit so adding more ports wouldn’t gain you anything in this regard anyway.
“So that VLANS share the same bandwidth is a non-issue for the use-cases intended for such a device.”
Actually … having pfsense do the VLAN splitting on trunks is a “lot” more
expensive than having extra interfaces and splitting your VLAN’s untagged over them.
On old or power conservative devices this will become a serious bottleneck.
I myself acquired an old Lanner FW7522b (cel 1,00 ghz, 1 gb ram), to get my feet wet with pfsense.
In my setup I have VLANS for wired, wireless and mgmt.
VLAN to VLAN traffic on the same trunk/interface yielded 13.5 mbps while
splitting it out across different physical interfaces brought me my expected line-speed (100mbps).
So … bear this in mind when deciding on low power devices.
I’d guess that that would depend on what hardware (or drivers) you are using. That seems excessive though. I have not tested the limits but I have no problems routing 100 mbps on my old intel NUC with its single LAN-port. And I am running xenserver on the NUC and virtualizing pfsense at the same time as running a bunch of other VMs with various loads.
I’m quite inexperienced, but have soon up a handful of pfSense incarnations this calendar year. Was evaluating OPNsense VM on my ESXi host, but currently have an old Sempron with 2GB RAM and intel Pro 1000 quad port as the edge device for my budding, wannabe lab. I’m lazy and keep going back to my little Edgerouter-X. For fifty or sixty bucks I expected to outgrow it almost immediately, but still haven’t donated it to my parents… yet.
Excited to hopefully sit down this weekend and try to dive into 2.4 and perhaps finally upgrade the ERX. I could potentially see a use for this in meager infrastructure. PoE would be clutch, though.