HPE EC200a Test Configuration
For our solution we had a fairly basic configuration:
- System: HPE ProLiant EC200a
- CPU: Intel Xeon D-1518 (onboard)
- Memory: 2x 32GB DDR4-2666 ECC RDIMMs (64GB total)
- SSD: Intel DC S3700 400GB
- iLO License: iLO Essentials (Stanard) iLO Advanced (Licensed)
This is not an extreme system configuration. The low-power 4-core/ 8-thread CPU, small footprint, and the proprietary expansion options limit how much we could do with this system. We are going to note here that there was a HPE TM200 solution that was very similar. The TM200 not only had the Xeon D-1518 but also the Xeon D-1537 8 core/ 16 thread part.
HPE EC200a Management
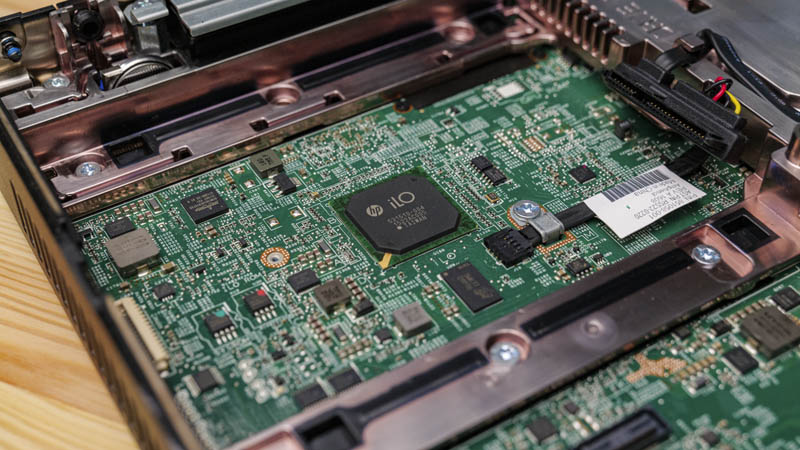
Onboard we get a HPE iLO 4 Baseboard Management Controller or BMC. This is a standard iLO management solution that we would find in other HPE servers.
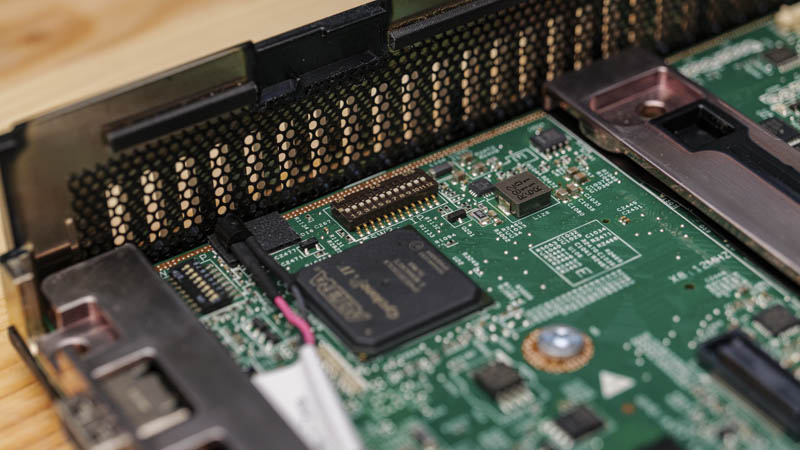
One of the really interesting features that one gets with this system is the HPE switch array that allows one to do things such as reset the iLO controller but also to make the system more secure. For example, these switches can be used to lock the configuration to prevent the tampering of the server. In edge devices, this type of security solution can be extra important as there are additional physical security threats present at the edge that are not present in a data center.
The look and feel of the EC200a’s iLO 4 controller are similar to other ProLiant offerings so users of HPE data center solutions will be very familiar with this solution.
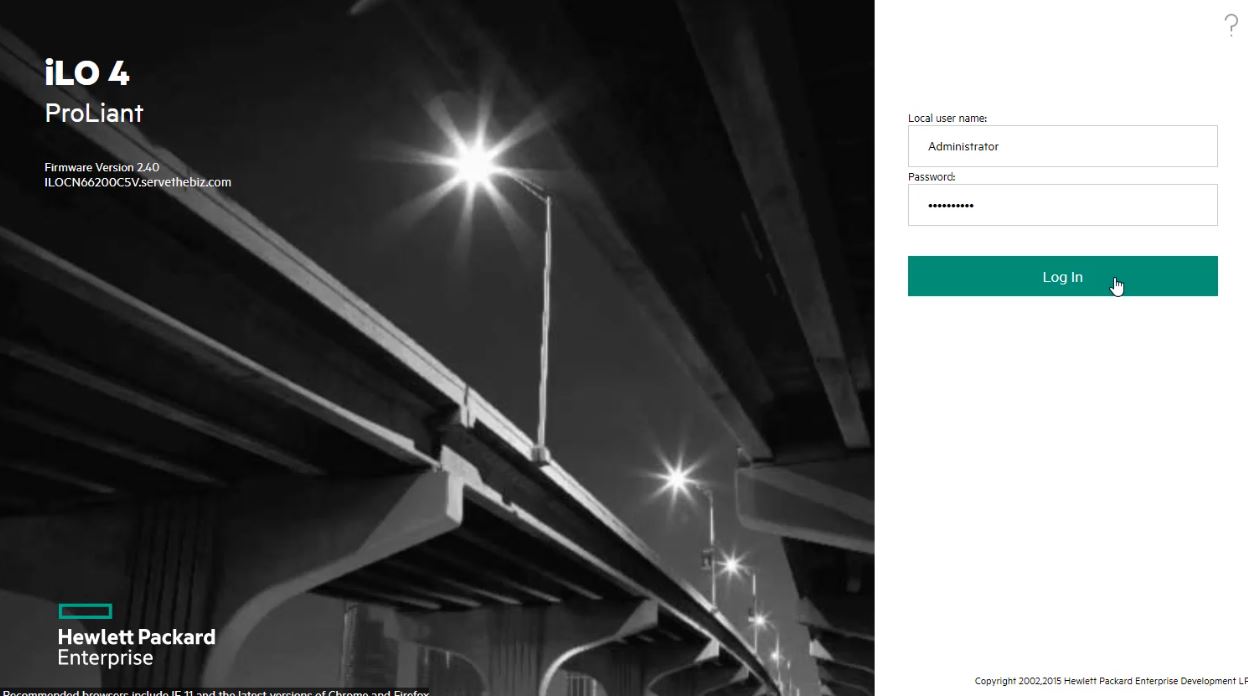
Our system has iLO 4 Essentials loaded by default. HPE segments their firmware into different levels so many of our users will want to find a reseller to gain access to iLO Advanced rather than iLO Essentials to get even some basic functionality.
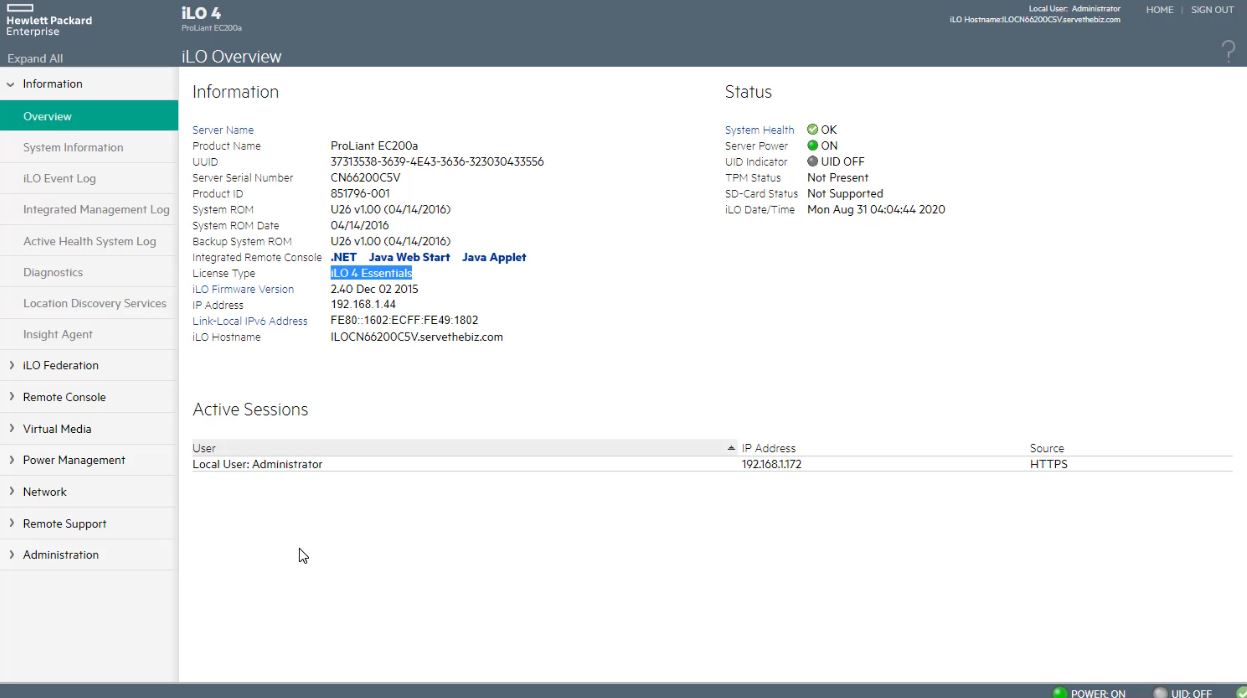
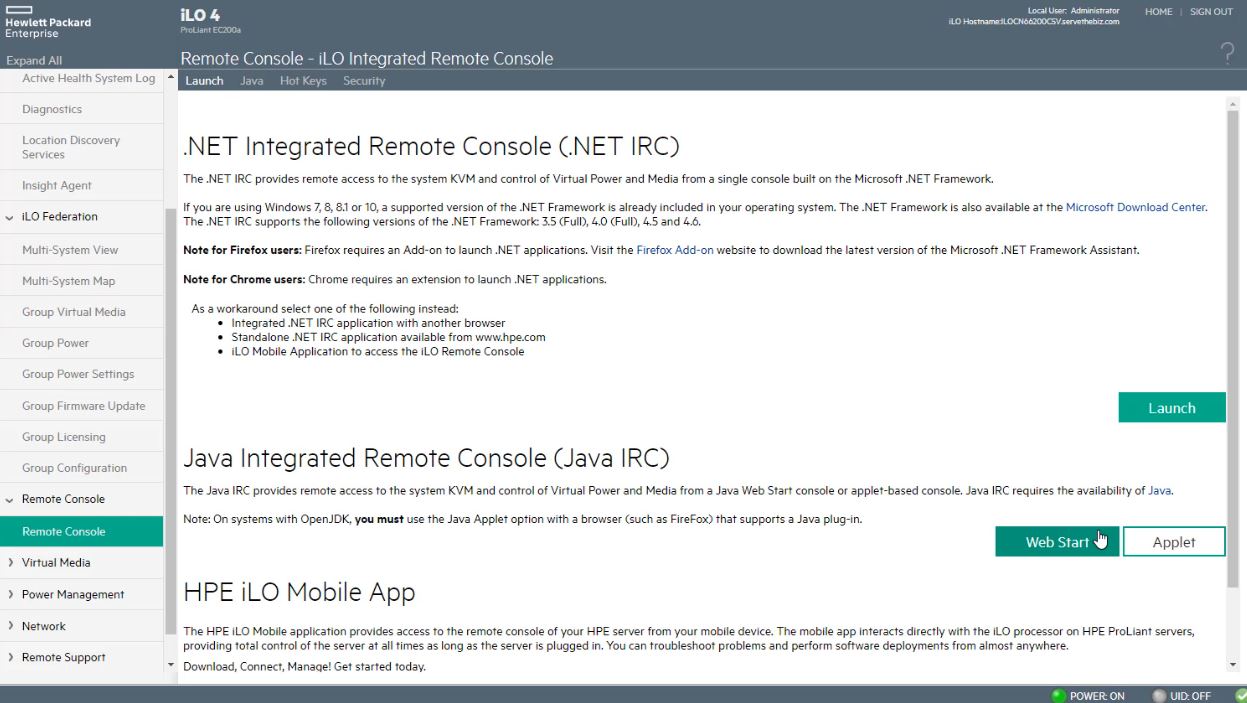
A good example of this is the iKVM feature which is much more limited in the iLO Essentials versus Advanced. Since this is iLO 4, we have the .NET and Java consoles, but not the iLO 5 HTML5 iKVM feature.
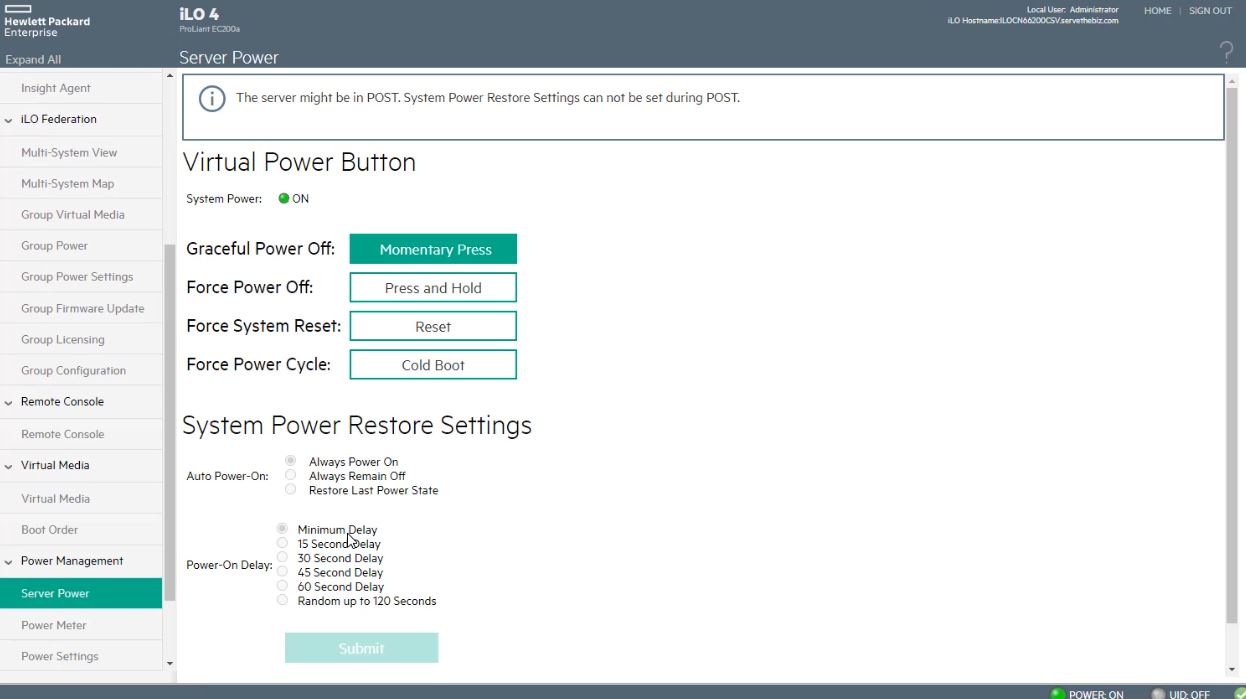
While those features may not be class-leading today, HPE does have some of their great features such as the way they handle remote power cycling in iLO 4 so there are trade-offs.
One area that is perhaps more important than the actual operation of the remote management solution is the firmware situation. To update the iLO or system firmware one needs access to the HPE support site and an active maintenance agreement for these machines. Other vendors tend to make access to updates freely available.
In a review like this, with a product late in its lifecycle, we can see the impact this has. For those with 5-year support agreements, their systems can be updated and secure today. For those with 3-year support agreements, they may not have access to updates leaving them less secure.
One can argue that HPE should charge for keeping these systems up-to-date. On the other hand, these are much higher margin machines even without the support agreements and the impact is not just to those running systems. Instead, insecure systems lead to potentially compromised systems hurting third parties. We will let our readers weigh in on whether it is the responsibility of the system’s operator to pay for security updates or if HPE should provide them as a good corporate citizen. The IT industry uses both models, however, while HPE has been losing relative data center share while white box solutions that do not have this paywall update polity are growing in overall data center share. Let us also be clear that this is a support contract atop the likely paid upgrade to iLO versions.
Next, let us move to performance before getting to power consumption, noise, and our final words.




This seems similar in spirit to the recently reviewed HP EC200A.
This is superior to the EC200A along all the dimensions that one would be considering these units (primarily CPU performance, networking, IPMI licensing cost), but the latter has been available fairly cheaply used.
Now that it’s been a few years, what does everyone seem to be using this for? It’s almost like a mini/micro pc in a larger form factor so it can take bigger physical drives.