A question we get asked a lot at STH is “what is a baseboard management controller” or “what is a BMC?” In this article, we are going to answer some of those questions for you. We are going to show you what a BMC looks like. We are then going to discuss common BMC features and the impact of the BMC.
What is a Baseboard Management Controller or BMC?
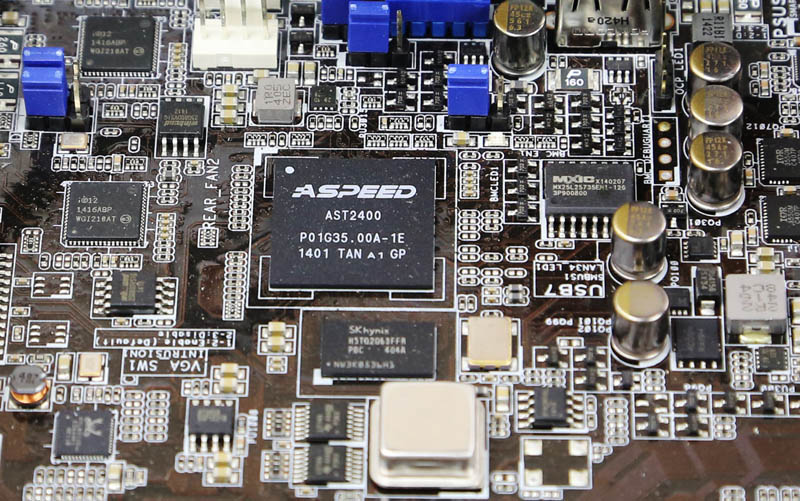
A baseboard management controller, or BMC, is a small computer that sits on virtually every server motherboard. Other components such as higher-end switches, JBODs, JBOFs, and other devices now include BMCs as well. The largest vendor for BMCs today is ASPEED whose AST2400 BMC is pictured below.

The BMC is usually an Arm-based SoC with graphics and control logic built-in. Vendors have used non-Arm solutions, but the current king of the market is ASPEED and its AST2500 series controllers that are used in servers from major OEMs to hyper-scale switches. These chips are often found on motherboards alongside some nominal amount of DRAM. SoCs are often accompanied by flash storage onboard, and various I/O.
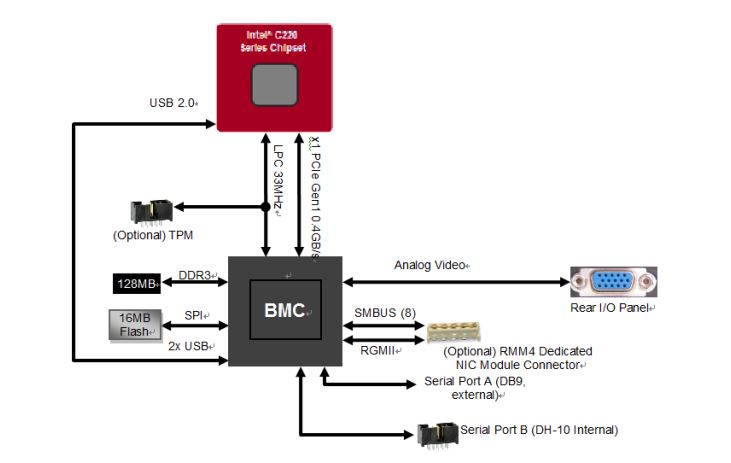
For our more technically minded readers, here is an Emulex Pilot 3 diagram on how the BMC hooked into the Intel chipset on an Intel S1200V3 motherboard.
Here is the official ASPEED AST2500 system diagram:
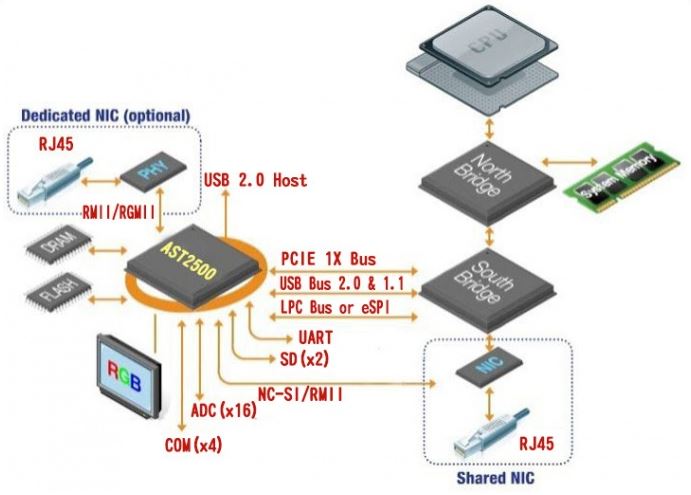
Key here is that the BMCs can utilize either shared or dedicated NICs for remote access. They also have multiple connections to the host system providing the ability to monitor hardware, flash BIOS/ UEFI firmware, give console access via serial or physical/ virtual KVM, power cycle the servers, and log events.
The analogy that I typically use when describing a BMC is that it is similar to a small Raspberry Pi type device that sits in a server in order to control the larger server.
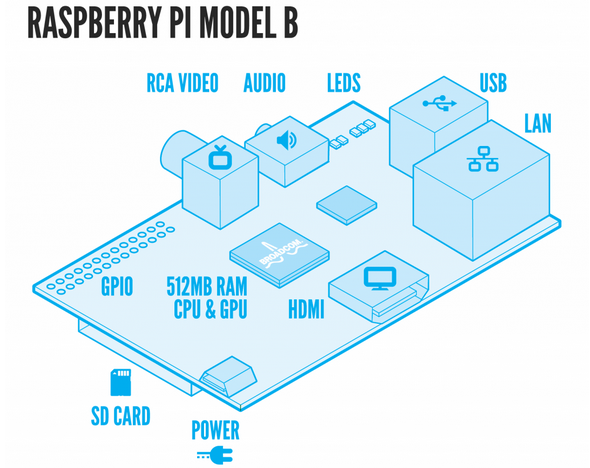
If you look at the BMC diagrams, and a Raspberry Pi diagram, there are quite a few similarities.
Why are Baseboard Management Controllers or BMCs Used in Servers?
Baseboard management controllers are used in servers to perform the tasks that an administrator would otherwise need to physically visit the racked server to accomplish. Some of the more common use cases are power cycling a server and monitoring fan speeds/ component temperatures, and hardware failures.
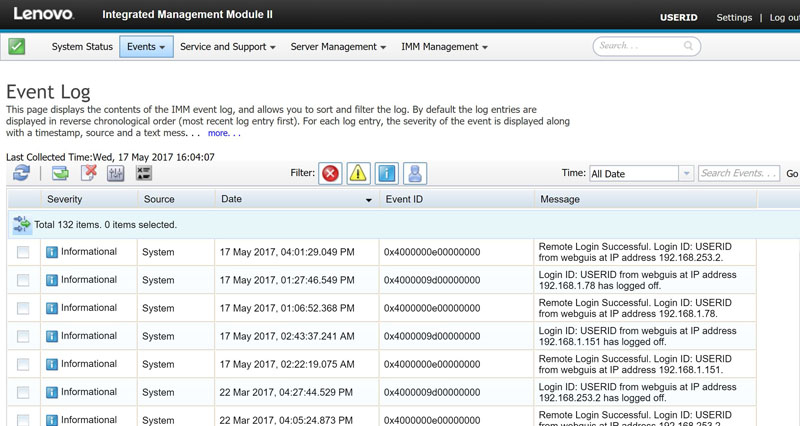
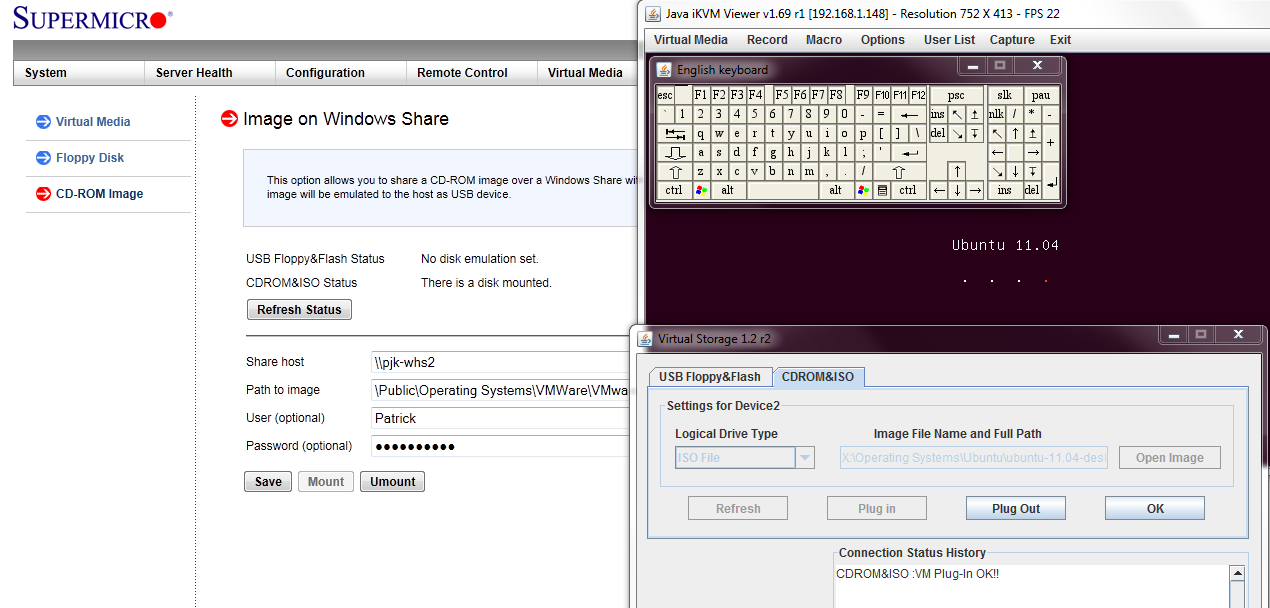
Many enterprise BMCs include iKVM functionality. Instead of physically going into the data center and hooking up a keyboard or monitor, one can get a Java, ActiveX, or HTML5 browser-based keyboard, video, mouse, remotely. The trend is toward HTML5 browser-based iKVM implementations. This single feature allows an admin to do low-level tasks from anywhere instead of having to physically visit the data center.
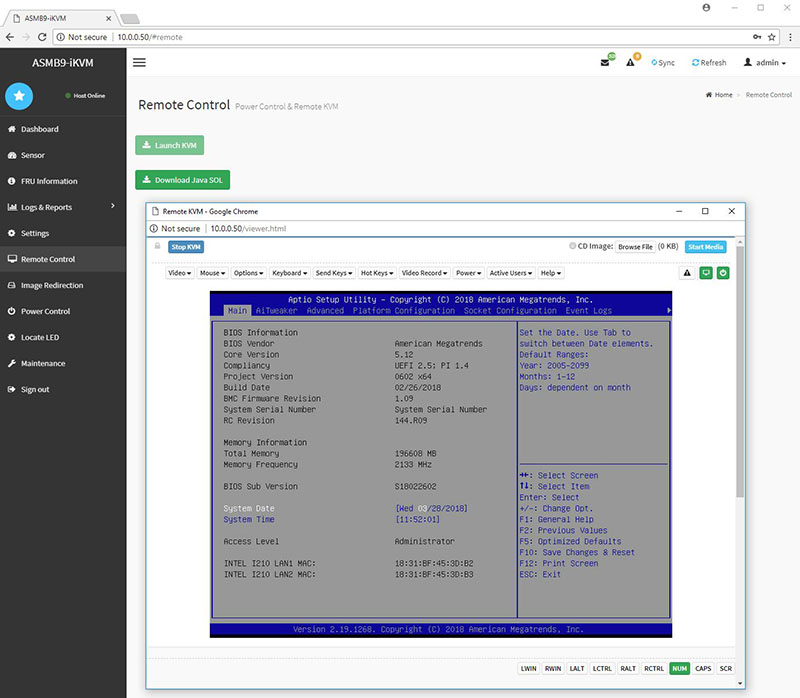
Aside from the KVM features, these BMCs can also load installation media over the network. With BMC access, one can use virtual media features to, for example, mount an OS installation ISO.
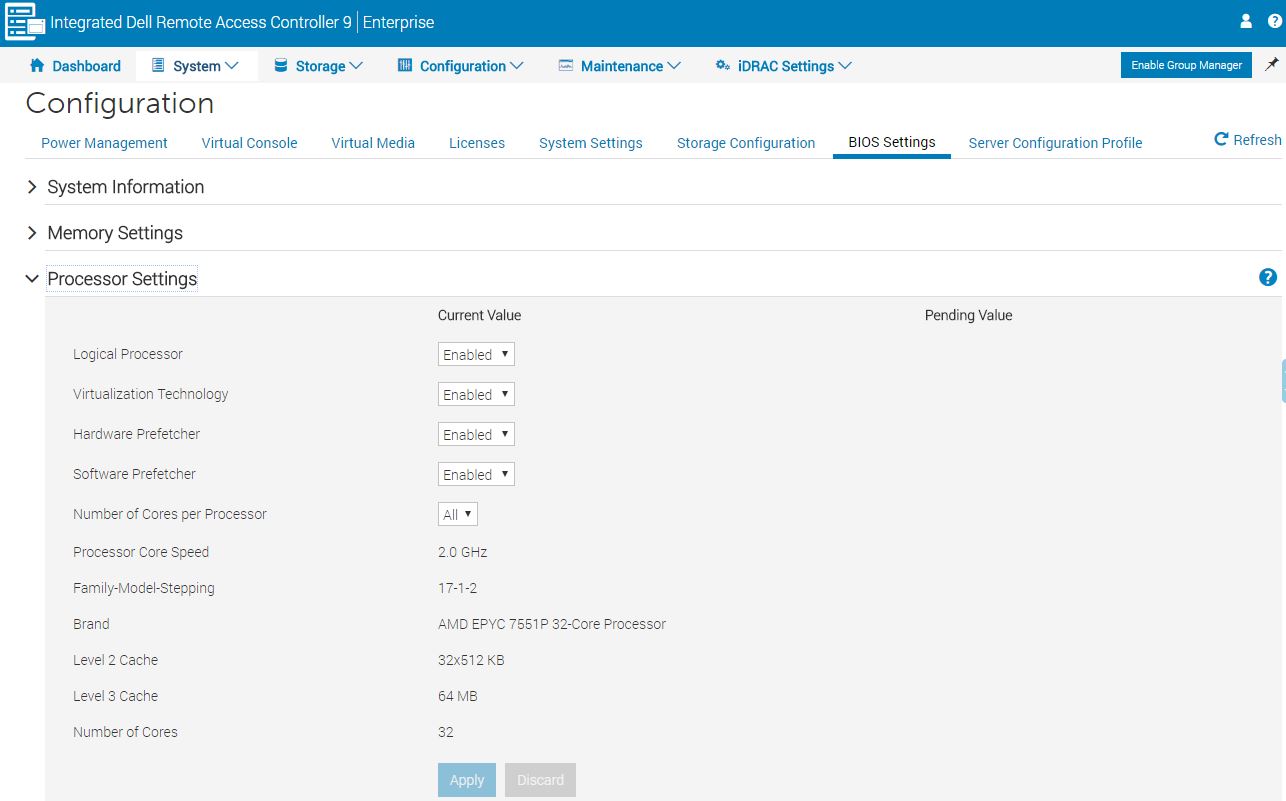
Some of the more advanced implementations, such as Dell EMC’s iDRAC, allow for low-level changes like BIOS settings changes directly via the web management pages.
BMCs are important because they allow not just single server administration, but armed with IPMI and Redfish APIs, the ability to manage clusters of servers at a time. For example, when a cloud provisioning system needs to reboot a server, nowadays it does so via an automated call to the BMC on that server.
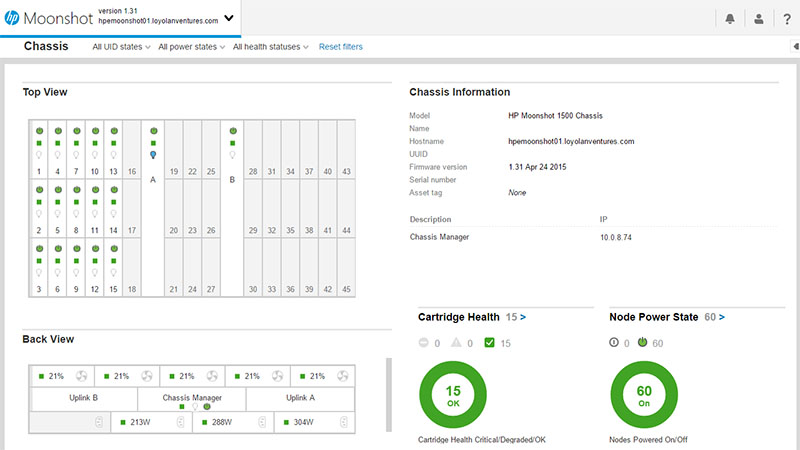
In summary, the baseboard management controller, along with standards like IPMI and Redfish, have provided the basic functionality to make large-scale server farms possible, and small server installations easy to manage. On an individual server basis, having a fully-featured BMC and management software removes the need to service a machine onsite except in the case of physical changes to the server (e.g. a hard drive replacement.) Software leveraging BMCs make vast quantities of servers uniformly and remotely manageable by relatively few remote resources.
Giving remote access to a system via a BMC and software stack is a well-known security vulnerability, but in 2018 most server vendors we talk to say that BMCs are in “high 90’s percent” of servers. BMCs are the ultimate security liability because they extend what had been in the realm of physical administrative access to a remote network connection. At the same time, BMCs have helped drive trillions of dollars of economic activity by making large compute farms manageable and therefore deployable.
BMC = IPMI Right?
This is a common misconception that a BMC is a server’s IPMI. IPMI, or the Intelligent Platform Monitoring Interface, is the standard for remote server administration. Baseboard management controllers are the physical chips that implement IPMI. Again, think of the BMC as a Raspberry Pi, where the various I/O elements are used to provide IPMI functionality.
BMCs are also an integral part of the next-generation management tooling.
IPMI v1.0 is Over 20 Years Old
The fun fact for our readers, IPMI v1.0 came to fruition in 1998. We are now on IPMI v2.0 (first out in 2004) and have next-generation Redfish standards being implemented. At the same time, this is easily one of the most important data center innovations in the last 20 years.
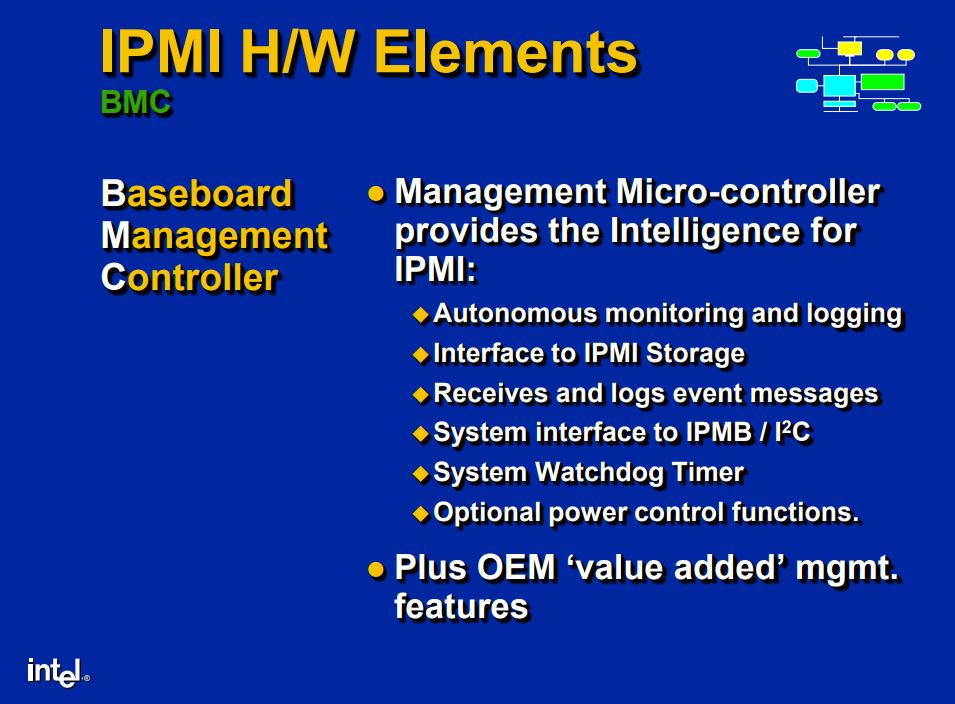
Baseboard management controllers have been part of the IPMI ecosystem since v1.0. Here is a presentation from Tom Slaight and John Graf at Intel dated September 16, 1998:
The BMC has been an IPMI component for over two decades which is why people often refer to the BMC as the “IPMI controller.”
Final Words
STH takes care to highlight management solutions of every server we review. One may have noticed that we highlighted a number of different vendors and their BMCs / software stacks in this article. Out-of-band management for servers is truly one of the largest innovations in the data center. Instead of having to physically visit a data center, plug-in or switch a keyboard, video display, and mouse or power on/ off a machine, one can now do it remotely. One can use BMCs to remotely monitor and manage large clusters of servers and automate IT processes. At the same time, even a single colocated server can benefit from a BMC by dramatically cutting remote hands costs. While BMCs present a surface that rightly is the focus of many security researchers, it is also a technology which underpins modern infrastructure from the smallest to largest server deployments.


Anyone has experience on getting the iKVM to work when using a discrete graphics card next to the onboard AST2500? (no monitor connected to ast2500)
I’m unable to see the bios screens etc. (asus x299 pro/se motherboard)
Hi Navi, have you set the onboard graphics to primary and add-in card to secondary graphics in your bios or UEFI?
Hi,
The discrete graphics card is set to primary.
Hi,
Great article. I have a home built server based on a Asus WS C621E SAGE motherboard. The server has also 4 NVIDIA GPUs , but none is connected to a monitor, nor the integrated VGA. I’d really like to be able to enter the BIOS setup as you show in a screen shot in this article. The BIOS setup should be entered supposedly by pressing
during POST. Unfortunately, for as mush as I try, I cannot enter the BIOS setup. On power-cycling the iKVM shows momentarily the “ASUS In search of incredible logo” past that the screen does not show anything.Is there anything I am doing wrong?
Thanks for any advise,
Andrea
very nice article which gave me the perfect understanding and differences of various terms like BMC and IPMI with appropriater picture of hardware and the diagrams for co-relation.
thank you
Really useful, succinct, thanks.
A really good article. Very well explained.
Thank you.
IPMI doesn’t seem to work in VMware environments. Anyone know how to get IPMI data in ESXi version 6 or 7?
@Priya
On Asus motherboards (Workstation MB with ‘WS’ in the name), you MUST select the ‘onboard video card’ as the primary video card if you want to enter BIOS or to manage server through the IKVM
For example, on motherboard Asus X99WS/IPMI with ASMB8-iKVM (using an AST2400 chipset), it’s written in the documentation : E10970_ASMB8-iKVM_UM_V2_WEB.pdf
P96 / appendix :
A3 TROUBLESHOOTING
“The ASMB JAVA console only works with the onboard VGA. Other add-on video cards may
not properly display the ASMB JAVA console.”
After a lot of tests, ONLY the internal VGA card buil-in with AST2400 in ASMB8-iKVM car display the BIOS and the system correctly on the iKVM (But mouse and keyboard are working on the black screen and clicking is doing things you cannot seen in the BIOS … DANGEROUS !)
Regards,
nbanba
A really good article. Very well explained. Thank you!!