TP-Link Omada VPN Gateway ER8411 Performance
First off, we tried just passing traffic through the gateway at full 10Gbps speeds to see if we could do that with IDS off.

This was not an issue at all and the gateway passed standard HTTP(S) bidirectional 10Gbps of traffic with ease.
The next step was turning IDS and IPS onto high to see if there would be an impact to the performance.

A few things to note here. First, the throughput dropped by about 2Gbps. Also, you will see that as the users/ connections scaled, we got large latency spikes and so CyPerf backed off the device.
We then added deep packet inspection to the setup.

There was really not much of a change here versus just turning on the IDS/IPS, but we wanted to see what checking the box on the DPI setting would do.
We then tried our standard low-end STH gateway device review 11 app mix of ChatGPT, Google Drive, Google Sheets, LinkedIn, Netflix, Office365 Outlook and Calendar, Reddit, X.com, and YouTube. With all of the security features, turned on, we hit around 10Gbps of traffic.
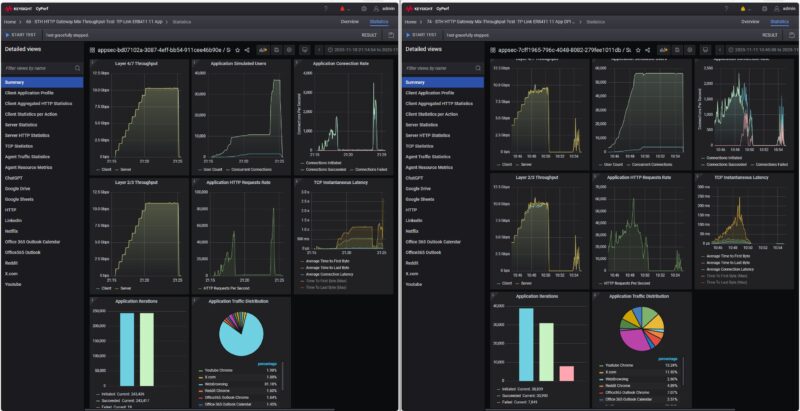
When we turned on the security features onto high, we saw something really interesting. First, the maximum throughput dropped by around 1-2Gbps again. The bigger change is that after some time, some of the traffic failed, and then the device just stopped passing traffic. After a few minutes, the traffic picked back up, but at a much lower rate then we were still getting failed connections.
We ran this a few more times, restarting the unit between the runs. We also wanted to turn the DPI feature on as well to see what would happen.

With the DPI setting turned on, we lost some performance again, but we saw a similar pattern where connections were getting dropped then a trickle of traffic would get through.
Just as a note, we did not turn on the attack profiles for this, it just happend repeatedly during our testing and we thought it was a really interesting result worth sharing. Of course, running a gateway at 100% for this long would create a rough user experience. At the same time, it shows why it is important to use real-world traffic when testing firewall features.
TP-Link Omada VPN Gateway ER8411 Power Consumption
In terms of power consumption, at idle we saw around 12.3W, which is decent for at 10Gbps gateway.

With one 1GbE port connected, we got 12.6W.

Connecting a SFP+ to 10Gbase-T device, we saw an increase of 1W to 13.3W. We generally only had noise in the 36-39dba range during our testing in a 34dba noise floor studio.

Overall, this is decent power consumption and what we would expect from a device like this.
Final Words
What a cool review on a number of levels. First, we found a device that is 10Gbps capable and certainly delivered that with simple traffic. We were able to see how turning on some relatively basic firewall features had a direct impact on the performance. We also saw something really neat as the combination of applying the firewall features and the real-world traffic under high-loads we managed to get the TP-Link to stop passing traffic. Again, this was without adding attack profiles into the mix which made it really interesting.

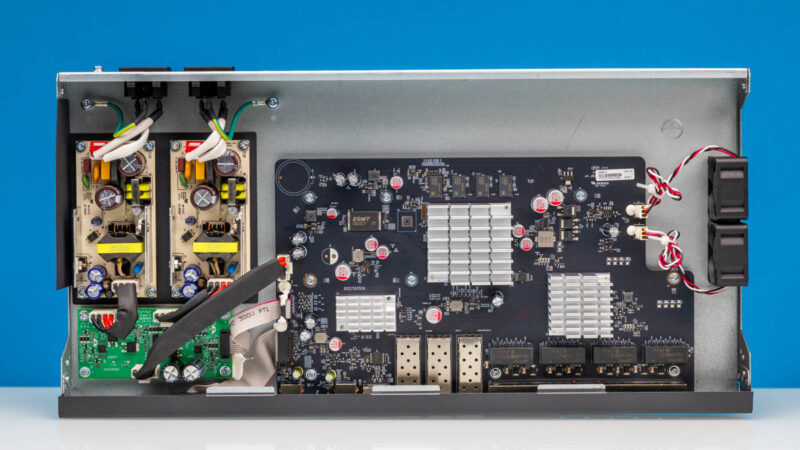
In terms of the hardware, TP-Link has a decent design, but we wish it would switch to screws or clips so anyone can inspect the hardware. At least that will let folks inspect their own hardware, which would be useful given some of the pressure on TP-Link.
Hopefully folks find this interesting. This is a great case of how using a (significanly) higher-end traffic generation tool is getting us more interesting data. We will keep stepping up the intensity in future reviews, but we thought this was a neat box to review.
Where to Buy
Here is an Amazon affiliate link to what we purchased.



There is a 4-pin serial header to the top left of the main chip/heatsink – be great if you were able to grab the boot log from devices and post them up so folks can see what they run ‘under the hood’
I think it is a somewhat expensive product for the feature set offered. 4 years ago I bought a Zyxel XGS1250-12. It is a very similar device (1x SFP+, 3x 10GBase-T; 8x 1G) and also a managed switch. It has been really solid and has worked well. I think it sells for around $179 these days.
Wait…
This is a “VPN Gateway”? Did I miss the part where you test VPN features? Or even describe what’s on offer?
Also I think I missed the conclusion where you said “this device is unsuited for purpose because it locks up under heavy load”.
Sorry, I should also say, it’s good that you uncovered the issue. I just feel like your reviews often leave way too many questions unanswered.
Unless one is used to the constant enthusiastic enthusiasm for new technology enthusiastically present on this website, it is easy to confuse an unfavorable review with a favourable one.
I like the enthusiasm but wonder why the network starts lagging. Does the hardware overheat under load?
I have a lesser version of the same Omada family. Same firmware and GUI. Another reviewer said its a custom GUI over OpenWRT, but I didnt see any proof of that.
As for the testing stall, the ARM Cortex was overheated and went into a deep down throttle waiting for it to recover to a normal temp.
So far it has passed all of my IPS testing, but that doesn’t rate it as impervious to attack.
I am load balancing 3 WAN’s with it, not perfect, but fine for my needs.
@Eric Olson: Its not really about the results, its the fact they have a cool new tool to play with and want to show you what it does.
This is not the Tolly Group.
Has a section about noise, not a single word about noise. VPN router review without VPN. Why do STH reviews becoming sloppier every day?
I didn’t realise these had gone up in price. I bought one at launch in November 2022, and it was $350 back then.
Most people don’t use the built-in web UI – instead, they use an Omada controller. You can get a hardware controller, or self-host it in Docker.
One thing worth noting: It took them a very long time to add an IPv6 firewall. For about a year after release, IPv6 was entirely unprotected – all inbound ports open to every device on your LAN!! Very poor security for something that’s supposed to be focused on the prosumer/SMB market. I turned off IPv6 until they finally released a firmware version with an IPv6 firewall (October 2023).
Apart from that, it’s a pretty good device and I’ve practically never had issues with it. Notably, it gets 10Gbps throughput even when using PPPoE (my ISP doesn’t, but it’s common in the UK for some reason).
Wonder how hard/cost it is to build a bare bones in China and then install your own OPNsense ?
@Tubz I suspect that that depends on your tolerance for hardware cost/power draw: x86 is going to be way easier to run OPNsense or other your-choice-of-OS on; but it’s not going to hit the same power envelope as a 4 core A-72; and unless there’s not just limited reverse engineering but proper support a weedy little ARM SoC is unlikely to manage VPN tunnels and IDS and the like at anything remotely close to wire speed since it is going to be leaning on dedicated offload for some functions.
If it’s not super mission critical; there are some great deals to be had by piggybacking on vendors who did the ‘get someone to ODM an x86’ strategy in order to get their product out the door, but only support the software for a limited period of time. I don’t know what the absolute best options in that vein are these days; but I’ve been pretty happy with the fact that a Lanner FW-7573 is quietly only $60 if it’s rebadged as a Talari e100; but there’s no way it draws less power than this thing, despite not being 10GbE.
Also of note is it looks like they were able to push it way past it’s advertised speeds. From the spec sheet:
DPI Throughput TCP: 5524 Mbps;
UDP: 3547 Mbps
IPS Throughput TCP: 4924 Mbps;
UDP: 4521 Mbps
@justsomeguy – Added a screengrab of the VPN tab. It is fair and should have been included. I think it missed the last edit of this because we are not publishing testing on it.
@Daniel – This is not the only one we have seen go up in price over the last six months.
@Eric – It is not a heat issue.
@spuwho – You are totally correct, this is not the Tolly Group.
@Multiple – On the VPN performance, that is really a can of worms. Do we just do IPSec? WireGuard? What about Fortinet and others that have their own clients? If we do all of those, what kind of traffic mixes do we push over them? What if one vendor is really good at one VPN type, but sucks at others, and we do not test that type?
Being fully transparent, I know folks want to see every feature tested. That is not really practical. Frankly, even the Tolly Group, which I have a lot of respect for and whose setup is close to what we now have, selectively tests features rather than testing every feature. They also did 2 reports between November 1, 2025 and January 31, 2026. We are doing 5+ hardware reviews per week at this point.
You may think, “if only they tested IPSec,” someone else may want to see MLPS, BGP, WireGuard, SSL VPN, in-depth QoS testing, different firewall tests, every level of firewall, and so forth. All are very valid desires. Realistically, though, testing one of these ties up test machines for, at a minimum, half a day with what we are already doing, and sometimes much longer. Nobody is remotely close to STH’s freely readable reviews in terms of breadth and depth of what we are already doing. There are two reasons for that. One, it costs too much to do even what we are doing. Two, it is an insane time sink.
We are going to keep adding testing over the next few months, but before we add a new test type, we usually back-test 24-50 devices to see if the test makes sense. Two units a day, given the timing, and the best case is that it takes 2.5-6 weeks to validate a new test. Then every review takes additional time to set up and run. If you just administer Cisco, for example, the setup steps for items are not the same on Ubiquiti, MikroTik, TP-Link, Netgear, and so forth. So doing so many vendors increases the time it takes to do them all because each needs its own procedure, down to the vendor, and often the product line. Even at the product line level from big vendors, we are finding small differences in how we have to physically set them up.
Also, that assumes everything goes right. Just yesterday, we found something failing our tests because we are pushing the gear so hard. We spent half a day validating that it indeed was an issue and giving the vendor diagnostic data on what we found. Hopefully, it makes it to a future firmware update and makes everyone’s experience better, but we are not getting paid to do this.
It is easy to say you want to see something. That is fair and good feedback. At the same time, we are spending a lot of time and money building this. We are not going to get to test every feature because there are simply too many in modern networking devices to do so if we also want to test a lot of devices.
@Patrick – That’s a very sensible answer. But I would suggest that for certain types of devices, there’s a balance point – if you can’t look at a certain minimum set of features, it might not be worth testing at all.
For example, this is a “VPN Gateway” (whatever that means) and not simply a switch. Sure, I’d want to know if the device can’t handle wire-speed switching, but if I’m buying it, it’s not so I can use it as a switch.
Your tests did do a good job in that they exposed some sort of major issue at high speeds. But if I understand correctly, it’s again using the device as a simple switch (or router?). Where’s the “VPN” part?
And yes, I get that there are lots of VPN options. Some are VERY different that others. Unless the device claims some sort of HW support for a particular type of protocol, I’d probably pick one lightweight (wireguard) and one heavyweight (IPSec? OpenVPN?) protocol, and test those.
I don’t think justsomeguy has any idea what he’s talking about. You didn’t say it was a switch. You didn’t test it as a switch. You tested it like you do gateways. I can’t imagine saying a review isn’t right if I didn’t know the difference between a switch and a gateway. Maybe he’s just trolling or an AI bot? I’d think an AI bot would know the difference if it isn’t using llama2
@justsomeguy they tested it with IDS/IPS. Not just as a switch. It would be considered a router or even a firewall (because of the IDS/IPS functions)
@MatsK… “See Figure 1”.
@J. Yes, you’re right, by the time I wrote the second reply I’d forgotten details that I should have gone back and checked. That’s my bad. My point though was that the “VPN” part of it wasn’t getting tested.
Interesting review, thank you.
What was missing here, after you found the performance drop under high load, is testing consecutively lower load levels to see if at some point the performance drop disappears. That would be helpful to establish a “functional level” of load. The way you left your finding standing out there unaddressed is somewhat unhelpful.
I hope this does lead to a firmware update. I’ve had this device for around 6 months and have not left on packet inspection because I noticed a few of these same issues.
Also some other issues with network speeds tanking with two models of their switches recently after firmware updates that only a reboot fixes. SG2210XMP-M2 and SG3428X-M2. Each has been through another newer firmware update and the problem has not been fixed.
I’ve built a few networks with omada gear because of the cloud management, and have been a bit disappointed lately waiting for things to work.
I love Omada stuff for my home… But there’s a reason I run OPNSense and then Omada gear for switches and APs…
I tried one of their 1Gbps VPN routers (ER605v2) because it had OpenWRT support, so as soon as I got it I flashed OpenWRT onto it and since then it’s been working a treat. It’s basically just a low power Linux box now that is capable of routing at wire speed, which is exactly what I was hoping for. On that one Wireguard is a little below wire speed (about 80% IIRC) but that wasn’t a problem for my use case. So if this one has the CPU power to route at 10G and it eventually gets OpenWRT support, I think I’ll probably grab one!
The Omada integration makes this interesting. I typically have Omada APs and switches, and always there is a seperately running OPNSense or OpenWRT router/firewall/VPN gateway. The question is, can the ER8411 replace an OPNSense or OpenWRT box/VM?